WhatsApp Web / Desktop
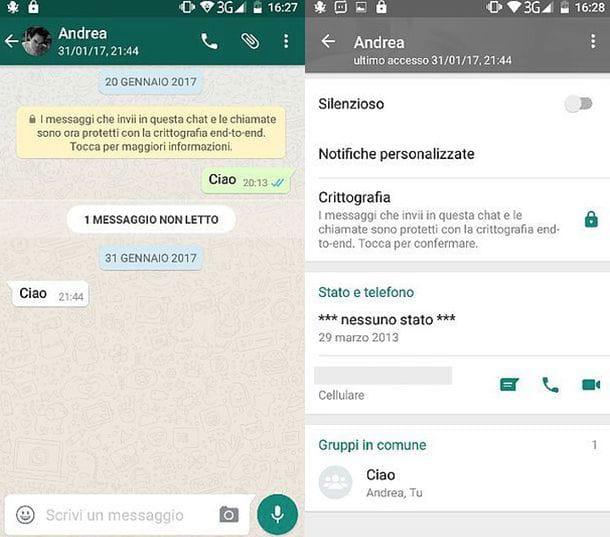
Strange as it may seem, one of the easiest ways to spy on another phone's WhatsApp for free is to use a service included directly in the application: I'm talking about WhatsApp Web which, as you probably already know, allows you to use WhatsApp on your PC through the browser.
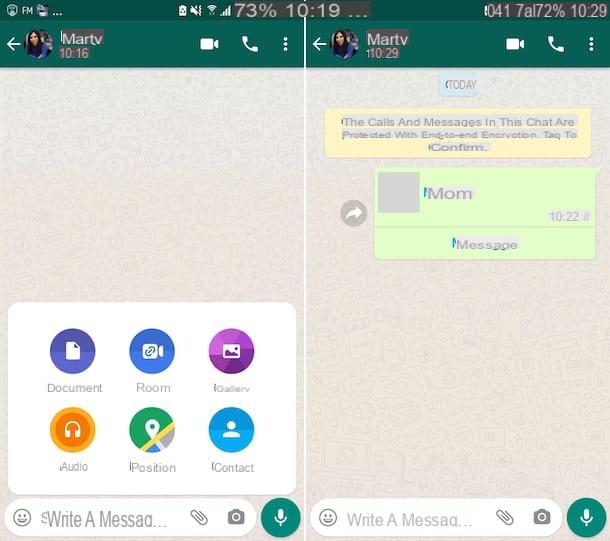
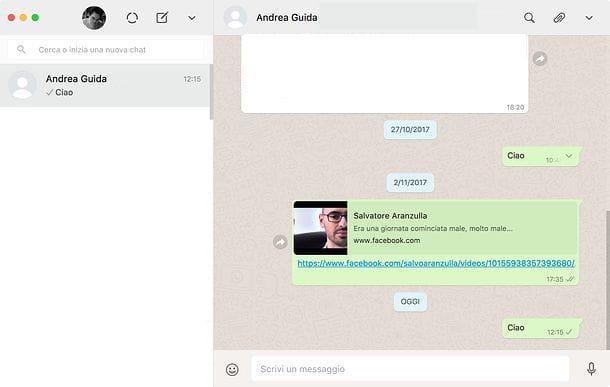
The operation of WhatsApp Web is extremely simple, and therein lies the rub! By connecting to the home page of the service and framing the QR Code that appears on the screen, it is in fact possible to access all your conversations and use WhatsApp as you do on a smartphone.
Where is the privacy risk in all this mechanism? I'll explain in a moment. If you leave the check mark next to the Stay Connected item, WhatsApp Web keeps access to WhatsApp open even for subsequent uses, so you no longer need to scan the code and access the chats directly.
Now, since WhatsApp Web does not require the connection of the smartphone and PC to the same wireless network (as long as the smartphone on which the application is installed is turned on and connected to the Internet, even via 3G / 4G network) , an attacker could steal with an excuse your phone, frame the WhatsApp Web QR code on your PC (or even on a tablet) and keep a gateway always open to your private conversations.
However, it must be recognized that, fortunately, spying on WhatsApp Web has become a little more difficult, since the service sends notifications quickly with each access made. In addition, if protection systems are active on the device of the user to be spied on through biometric recognition, it is not possible to activate WhatsApp Web without the consent of the owner of the device.
In addition, if you want to protect yourself even more, follow the tips below.
- Avoid lending your smartphone to other people - As trivial as it may seem, this tip is the most effective of all!
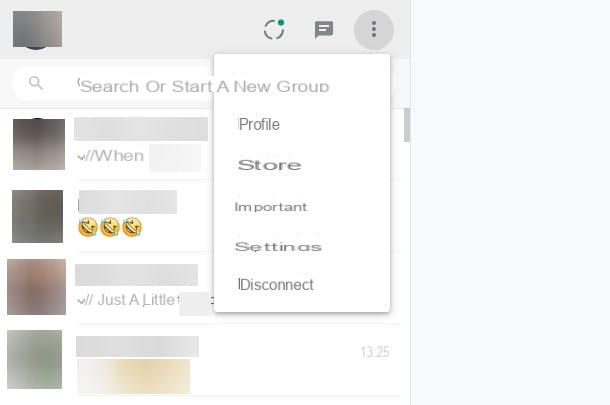
- Verify access to WhatsApp Web - by accessing the WhatsApp settings on your smartphone, you can verify the open accesses on WhatsApp Web and close them, so that the scanning of the QR code is requested again. If you use an Android terminal, you can verify access to WhatsApp by pressing the ⋮ button located at the top right and selecting the WhatsApp Web item from the menu that appears. If you use an iPhone, instead, you can do the same by going to the settings tab located at the bottom right and selecting the WhatsApp Web / Desktop item of the latter. Once you have identified the active WhatsApp Web sessions, you can close them by pressing on them or, alternatively, you can tap the option to log off all computers and close all access to WhatsApp Web at once.
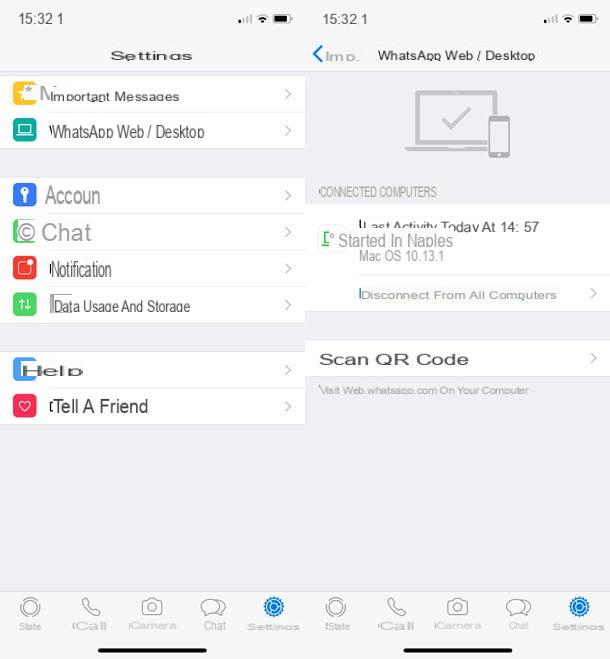
Note: The risks associated with WhatsApp Web also apply to WhatsApp Desktop, the official WhatsApp client for Windows and macOS. I told you about it in more detail in my tutorial on how to install WhatsApp on PC.
Spyware applications
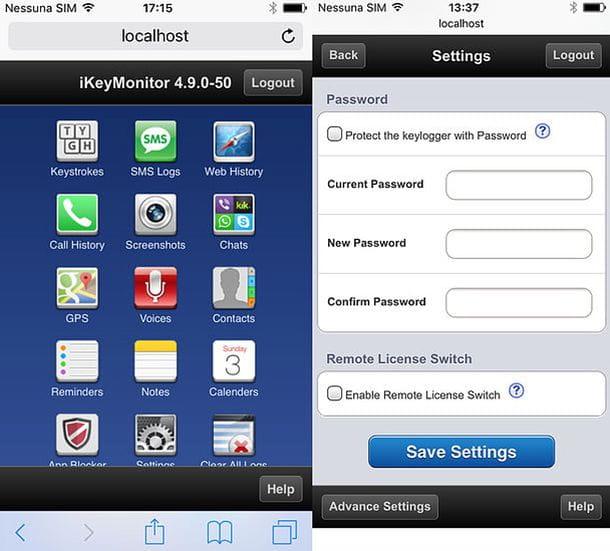
One of the greatest dangers to the privacy of conversations made on WhatsApp (and not only those) is represented by spy apps: they are applications that, as their definition suggests quite easily, hide from the user's eyes and track all his activities: the phrases and words typed on the keyboard (in this case we are talking about keylogger), the apps he uses, the websites he visits, his incoming and outgoing calls, and much more.
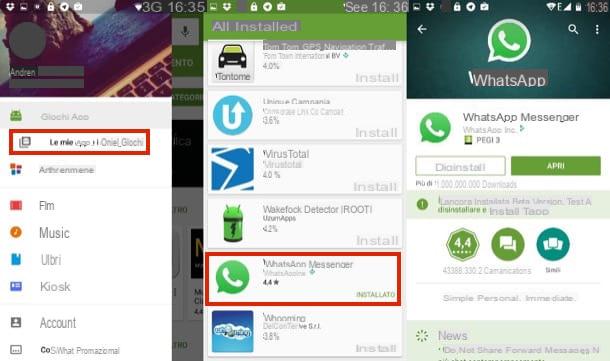
Unlike what one might imagine, many spying apps, although expensive, do not require advanced technical knowledge to use: just get the victim's smartphone, install them (often through the apk package on Android and through Cydia on iOS) and get comfortable. If you don't believe it, try to receive all the data collected by them directly on your PC or on your portable device. If you don't believe it, try taking a look at iKeyMonitor, one of the most popular spying apps on Android and iOS, which you can also try for free for a few days.
Spy apps, as mentioned, may be completely invisible to the user's eyes, but this does not mean that there are no clues that can give away their presence. If you suspect that your smartphone has been monitored with such a solution, implement the following tips to clear any doubts about it.
- If you use an Android terminal, go to the menu Settings> Security> Device Administrators and check if among the applications that have permissions to manage the device (so that they can deeply access the system) there are some "suspicious" ones. If so, disable them (by removing the check mark from their names) and uninstall them. If your device has undergone the root procedure, open the SuperSU / SuperUser app and check if among the apps that have active root permissions there are some that can be considered spy apps. Again, if you detect any "suspicious" apps, remove them from your smartphone by following the standard procedure for uninstalling Android apps.
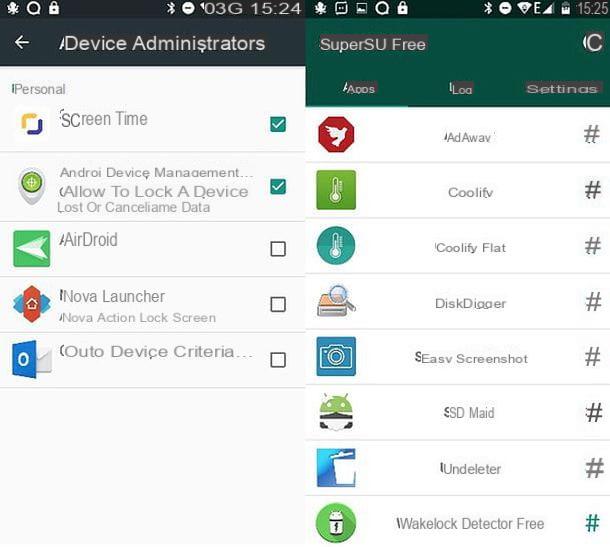
- If you are using an iPhone, go to the Settings> Device Management menu and check for custom profiles related to "suspicious" apps. If so, delete the profiles and associated apps. If the Device Management menu is not available, it means that there are no applications on your iPhone that use custom profiles. If you have an iPhone that has been jailbroken, open it also Cydia and check if there are spy apps among the installed packages: if so, select the packages and remove them from the phone by pressing the appropriate option.
- Open each browser and try to connect to the addresses localhost: 8888 and localhost: 4444. Some spyware applications use these addresses to hide their configuration panel, so visiting them may give away their presence.
- Open the dialer and try to type the code * 12345. This is another secret code used by spy applications to hide their configuration panel.
In addition to spy apps, you should also beware of parental control apps and anti-theft apps, therefore, legitimate apps, also available for free on Play Store that, if configured correctly, can become apps to spy on users' activities.
Some examples ?: Qustodio (Android / iOS / iPadOS) e
OF SCREEN
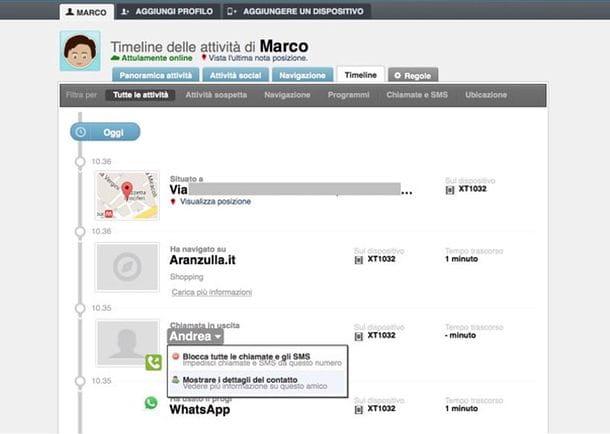
Also, the anti-theft apps can be used to locate the user and control your smartphone remotely. If you want to know more, I have told you in detail all the apps I just mentioned in my tutorial on how to spy on Android.
To counter the action of parental control apps and anti-theft apps, you can follow the instructions above and read my tutorial on how to remove spyware from your mobile.
Apps to detect access to WhatsApp
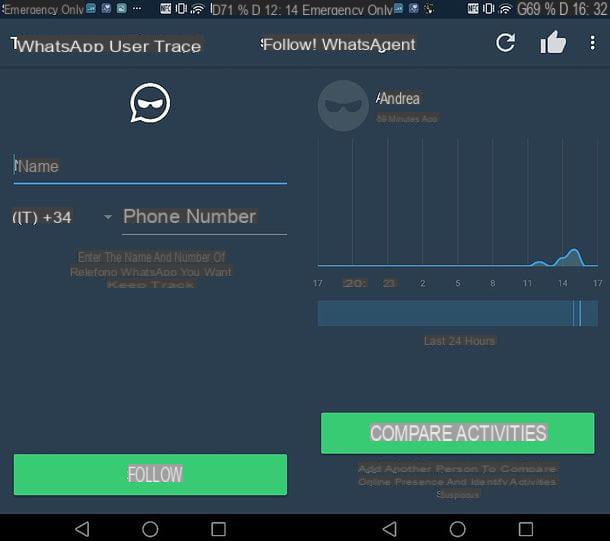
Until recently, there were some apps that, while not allowing you to directly spy on WhatsApp conversations, still posed a potential privacy risk by allowing you to do so. monitor whatsapp access by a user simply by typing in their phone number.
The apps in question were generally free to download and try out, but to take advantage of the data export feature and use them without limits, they generally required a subscription plan. Its operation was very simple: you had to start the monitoring app and type in the WhatsApp user number to be monitored. In this way, it was possible to see the WhatsApp access times of the user to be "spied on" and receive notifications regarding their activities.
The applications in question are no longer functional, fortunately I would say, but I thought I would warn you anyway not to ignore this potential risk (even if unlikely, a possible WhatsApp failure could allow a new life to this type of solutions. ).
MAC address cloning

As you probably know, WhatsApp doesn't allow you to use the same number on more than one phone. This means that if an attacker tries to activate WhatsApp using your phone number, despite having the smartphone at hand and being able to get the verification code on it, the app will continue to run on only one device, thus allowing the victim (i.e. you ) to immediately expose the identity theft attempt.
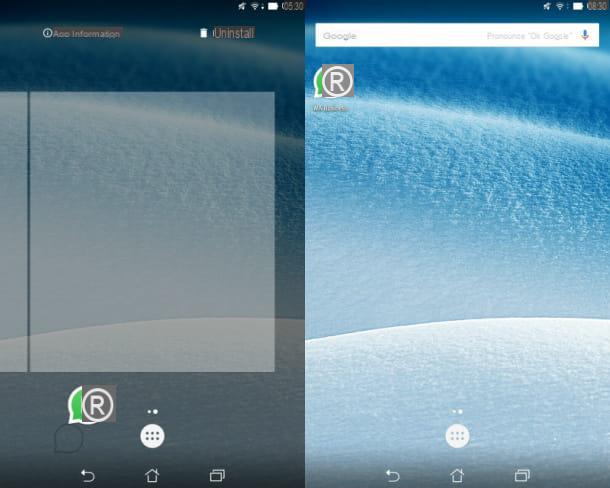
The recognition of the device on which a WhatsApp number is used is done through MAC Address, a 12-digit code that uniquely identifies all devices capable of connecting to the Internet. It is a very effective system, but not infallible. As I explained in my post on how to clone WhatsApp, in fact, there are applications that allow you to disguise the MAC address of your smartphone and therefore deceive the WhatsApp security systems by making the application believe that you are using the victim's phone and not another device. Among the applications in question I highlight SpoofMAC for iPhone and BusyBox and Mac Address Ghost for Android, but there are also other similar solutions.
The only way to defend against this threat is not to lend your smartphone to strangers. It would also be good to set a secure unlock PIN and hide the SMS screen from the lock screen (so as not to allow malicious people to discover the WhatsApp verification code without unlocking the device).
- To set a secure PIN on Android, go to the Settings> Security> Screen Lock menu and select the PIN item. Avoid using 'sequences', which are much easier to guess than PINs. To set the PIN on iPhoneinstead, go to the Settings> Face ID & Passcode or Touch ID & Passcode menu and select the Change Passcode item from the screen that opens.
- To block the display of SMS on the Android lock screen, go to the Settings menu> Security> Screen Lock, set a secure PIN and, at the end of the procedure, choose to hide only sensitive content. To block the display of SMS on the iPhonelock screen instead, go to Settings> Notifications> Messages and uncheck the item Screen Lock.
Sniffing Wi-Fi networks
As I also explained to you in my post on how to sniff a wireless network, is sniffing Wi-Fi networks is a technique that allows you to "capture" all the information transiting over a wireless network. It is effective when the "sniffed" networks are insecure and/or the systems that carry the data let the information pass clear, and this is not the case for WhatsApp.
WhatsApp, in fact, uses a security system called end-to-end encryption, which protects messages and all multimedia content passing through WhatsApp with "locks". This ensures that only the owners of the correct keys, i.e. the legitimate senders and recipients of the messages, can decrypt their content.
Simply put, even sniffing a Wi-Fi network and capturing WhatsApp data would be undecipherable to the bad guys (unless there are obvious flaws in the WhatsApp developers' implementation of encryption, which are unlikely but not impossible). In any case, I advise you to be careful and do not connect to public networks: always prefer private Wi-Fi networks and 3G / 4G networks of telephone operators.
If the issue related to end-to-end encryption bothers you and you want to learn more about how to encrypt WhatsApp, read my tutorial dedicated to the subject.