Every day I receive messages from people who are distressed by the idea that an attacker could enter their WhatsApp accounts, stealthily check them and spy on all their conversations. Are these fears unfounded or is there really a risk of someone sticking their nose into our messages? Let's try to find out together.
Below we will try to analyze some of the main techniques used by cybercriminals to spy on and check WhatsApp at a distance and we will discover what are the "counter moves" to be implemented to avoid ending up in their sights. I anticipate immediately that some risk really exists, on the other hand no computer system is 100% impenetrable, but we must not be paranoid.
By adopting common common sense rules and paying attention to those who use our smartphone, we can put "out of action" all attacks against WhatsApp without contacting professionals in the sector and without installing special software. But now enough to mess around, let's get right into the heart of the topic and begin to analyze the techniques used by cyber criminals to spy on conversations on WhatsApp: some are really very ingenious, as well as dangerous.
Identity theft on WhatsApp
To spy on our messages and check WhatsApp without our permission, cybercriminals must be able to disguise their real identity. They have to pretend we are, stealing our online identity. There are several techniques that can allow malicious people to steal our identities on WhatsApp, let's try to analyze a couple of them.
Web WhatsApp
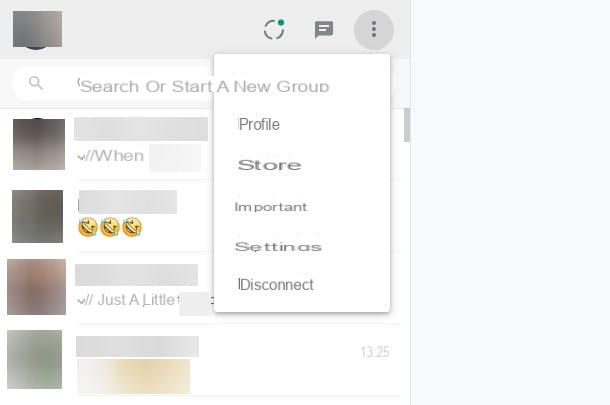
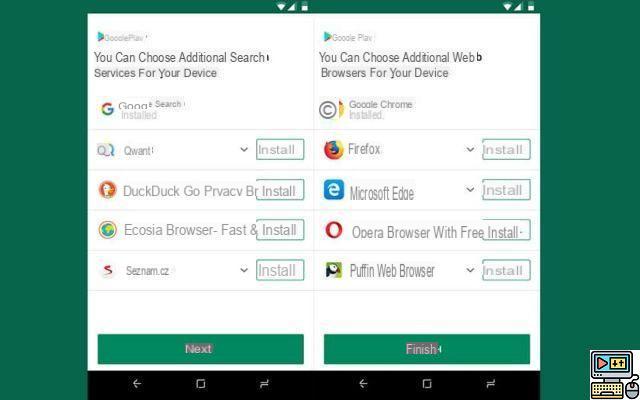
Web WhatsApp is a WhatsApp function that allows you to access the service via PC using any enabled browser, such as Chrome, Firefox or Safari. To use it, just connect to its main page, frame a QR code with the smartphone camera and leave the phone connected to the Internet (to any network, even the 3G / LTE one of your operator is fine).
Well, if an attacker manages to get hold of your smartphone, he uses it to access WhatsApp Web and at that moment he checks the box stay connected of the service, which allows the browser to memorize the user's identity, can obtain continuous access to your account without you noticing it, or almost. But we'll talk about this shortly ...
Mac address cloning
Another technique through which cybercriminals can perpetrate identity theft on WhatsApp is the "cloning" of the app by camouflaging the MAC address.
The MAC address is a 12-digit code that is used to uniquely identify all devices capable of connecting to the Internet, such as smartphones, tablets, PC network cards and so on. WhatsApp uses it together with the phone number to identify its users, then by cloning it - that is, by disguising it so that it appears the same as that of another user - it is possible to steal another person's identity and access their conversations.
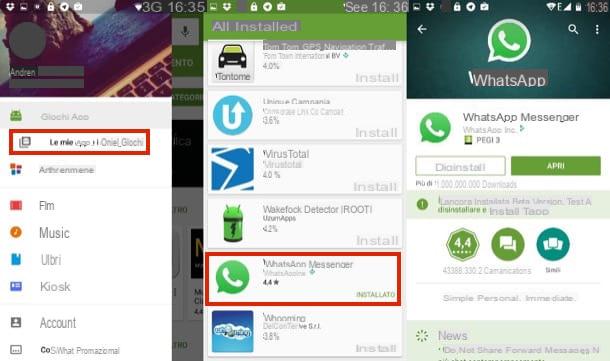
There are several applications that allow you to change the MAC address of the smartphone, such as BusyBox e Mac address ghost your android or SpoofMAC on iPhone. Using them is not complex, just root Android or jailbreak iPhone, but it takes a long time.
To carry out their "hit", cybercriminals must in fact discover the MAC address of the victim's phone (just access the menu Settings> Info of the latter), set the same code on your device, install a copy of WhatsApp and activate it using the phone number of the person to be spied on (on which the SMS with the WhatsApp activation code will be delivered).
Fortunately for us, this is a very complex procedure, it requires prolonged access to the victim's phone and a fair technical preparation on the part of the person who wants to put it into practice, however its potential effectiveness should not be underestimated.
How to defend yourself?
At this point, a question arises: how to protect yourself from those who want to steal our identity on WhatsApp? Considering that most of the techniques involve physical access to the victim's phone (at least initially), to defend yourself it is enough to put into practice some simple rules of common sense.
- Do not lend your smartphone to strangers and do not leave it unattended in public places.
- Set a secure PIN to block unauthorized access to the phone. On Android just go to the menu Settings> Security> Screen Lock I will select the voice PIN (Or Sequence, if you prefer to use a gesture instead of the numeric PIN), while on the iPhone just go to the menu Settings> Touch ID and Passcode I will select the voice Change codice.
- Protect your device with an unlock system via biometric recognition: this system not only prevents malicious people from being able to use your smartphone, but also from accessing WhatsApp / Web, as to scan the QR code and, consequently, to access the service, the owner's confirmation is requested.
- Prevent the display of SMS on the lock screen. This operation, associated with the use of a secure PIN, avoids the risk that an attacker can activate a cloned copy of WhatsApp using your phone number (as it will not be able to view the confirmation code that will be delivered via SMS to your device. ). If you have an Android smartphone, to disable the display of SMS in the lock-screen you have to go to the menu Settings> Security> Screen Lock, set a PIN or a gesture and choose to hide only sensitive content. If you have an iPhone you have to go to the menu Settings> Notifications> Messages and uncheck the item Show in “Blocco schermo".
- Monitor WhatsApp Web Sessions - We said earlier that if someone accesses WhatsApp Web using your smartphone you won't be able to notice. This is true, but only partially. By going to the menu Settings> WhatsApp Web of WhatsApp you can view all WhatsApp Web sessions active on your account and by pressing the button Log out of all computers you can deactivate them instantly. In this way all the “spies” connected to your account via WhatsApp Web will lose automatic access to the service.
Spy applications

There are now many applications to spy on cell phones. Some of them are very expensive and very difficult to use, while others are much more accessible and can be configured even with limited computer knowledge. Just think of the solutions for parental control or the location of lost devices, which are easily found on the official Apple and Google stores, in some cases they are free, but if properly configured they also allow you to spy on and control a smartphone from a distance.
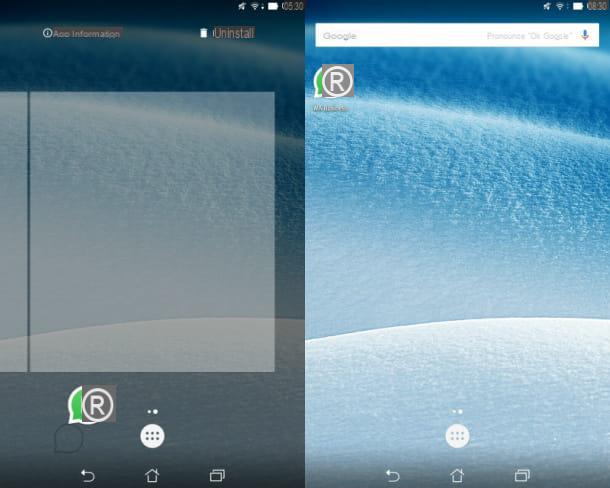
But how do we know if someone wants check WhatsApp remotely with one of these apps? Unfortunately it is not easy as most spy applications automatically hide themselves from all system menus, but trying doesn't hurt.
The first suggestion I give you is therefore to enter the application management panel of your smartphone (Settings> Apps> All your android e Settings> General> Storage and iCloud Usage> Manage Storage on iPhone) and check for suspicious names.
In case of negative result, if you suspect the presence of spy applications on your device, I'm sorry but the only solution that remains at your disposal is to format the phone memory. Find out how to do it in my tutorials on how to reset Android and how to reset iPhone.
Sniffing delle ret wireless

In conclusion, I would like to tell you about the wireless sniffing risk, which does not allow malicious people to check WhatsApp directly but may allow them to read your messages.
As I also explained to you in my post on how to sniff a wireless network, there are software that allow you to monitor wireless networks and "capture" all the data traveling on them. Among these there could also be WhatsApp messages, but fortunately there are protection measures that are applied automatically by the service and that should keep us reasonably safe.
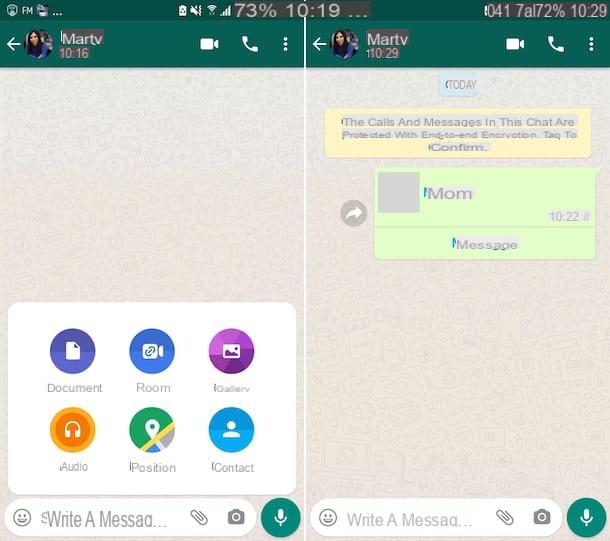
I refer to the end-to-end encryption that WhatsApp began to adopt at the end of 2014, which protects messages using a double key system: a public one that is shared with your interlocutor and serves to encrypt outgoing communications and a private one that resides on our smartphone and allows us to decrypt incoming communications. Such technology ensures that messages also arrive encrypted on WhatsApp servers and can only be decrypted by legitimate senders and recipients, however we cannot sleep completely peacefully.
Why? Because WhatsApp is a closed source application, we cannot fully analyze its source code and therefore we do not know if end-to-end encryption has been adequately implemented in the service. A test dating back to April 2015, for example, showed that only messages sent to and from Android were encrypted with the end-to-end system, on the other platforms an encryption system based on the RC4 algorithm was used which is much more vulnerable to external attacks.
Moral of the story? We need to trust WhatsApp and its security systems, or we can migrate to other open source messaging applications that apply end-to-end encryption transparently. Everyone has their own choice. Either way it is advisable avoid public Wi-Fi networks which, as we know, are a very popular hunting ground for cybercriminals.