This Thursday, our colleagues from Numerama revealed that Lidl's Monsieur Cuisine Connect cooking robot was in fact equipped with an Android tablet. However, it uses a version of the operating system that is particularly dated and which no longer benefits from security updates. What to fear for his safety?

The SilverCrest Monsieur Cuisine Connect robot
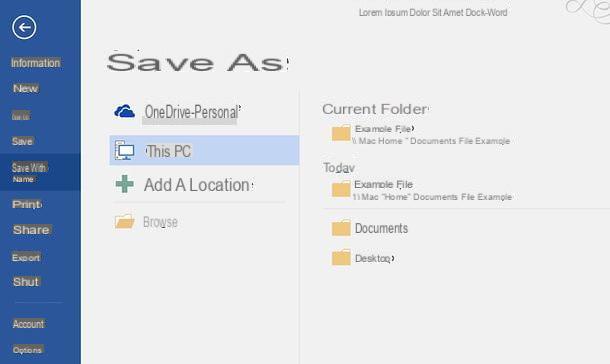
This Thursday, our colleagues from Numerama published the results of a survey around Lidl's latest food processor, the Monsieur Cuisine Connect, marketed under the SilverCrest brand. In particular, they revealed that the household appliance was in fact equipped with an Android tablet, but above all that it only benefited from version 6.0 of the Google system. Worse still, the last security patch installed on the tablet is that of March 2017.
What are the risks in terms of security in using a food processor with such an old version of Android, this is what we will see in this file.
Summary of the case
Launched at the beginning of June in Spain, SilverCrest's Monsieur Cuisine Connect food processor is one of the main competitors to the famous Thermomix. Equipped with a touch screen and an Internet connection, it allows you to program recipes and update yourself.
On paper, all is well. Only our colleagues from the Numerama site were able to discover that the food processor was in fact equipped with a real Android tablet. This is based on version 6.0 of the operating system, Marshmallow, released in October 2015. Above all, the last security update installed on the tablet is that of March 2017. Since then, nothing less than 19 other patches Security solutions have been proposed, each providing fixes, minor or major, to secure Android devices. Without these updates, the tablet therefore remains particularly susceptible to many flaws.
What are the unpatched flaws?
The SilverCrest Monsieur Cuisine Connect robot uses three means of connection: Bluetooth, Wi-Fi and the USB socket hidden behind a screwed hatch. So many ways for malicious applications to be installed locally or remotely on the food processor.
Twenty-six missing security patches
It must be said that since March 2017, twenty-six security patches have been deployed on AOSP, the Open Source version of Android. Among these, we can notably cite that of March 2019, for example, which corrected 11 flaws deemed “critical” for the integrity of the system. Not all of them apply to all devices, since some patches are specific to a hardware component that does not equip all smartphones or tablets. However, still in the March list, a "high" flaw could allow a malicious application to execute code with certain permissions. The flaw no longer exists thanks to the security update… for devices that have been patched. This is not the case with the Monsieur Cuisine Connect robot.

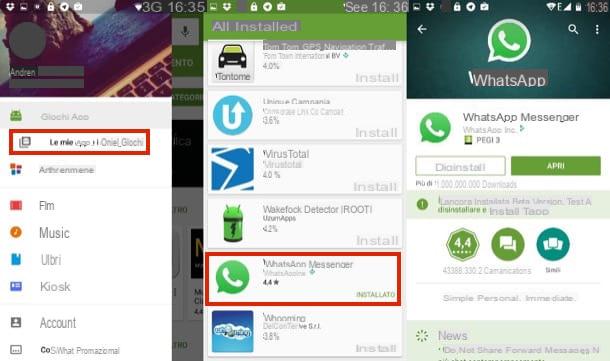
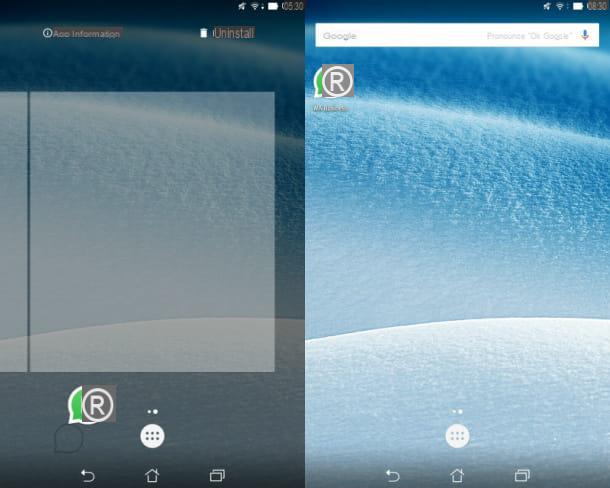
Lidl's Monsieur Cuisine Connect has an *old* version of Android
In June 2018, another flaw was revealed. This allowed a malicious application to be installed from a computer connected by USB or even Wi-Fi via port 5555. This flaw had been exploited in particular by a virus which installed a cryptocurrency miner on devices which had activated default USB debugging mode or wireless ADB debugging mode.
Flaws of this type, there are dozens that are identified and corrected every month by the Android Open Source project. So many flaws that can be exploited by a malicious application to hack a smartphone, a tablet… or a cooking robot, if it has not been updated. More worryingly, not only does SilverCrest's robot not benefit from security updates, but it also has a microphone. If this is disabled by default, it remains well connected to the system and is recognized by the tablet software. However, in the past, several security researchers have already reported on the risks of having a microphone on an Android device, especially for remote listening or recording.
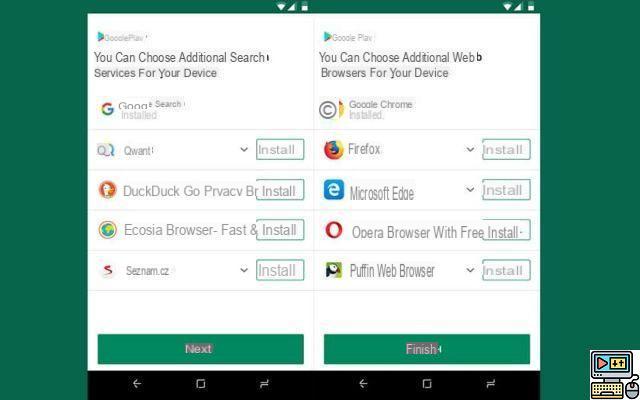
No Google services, so little protection
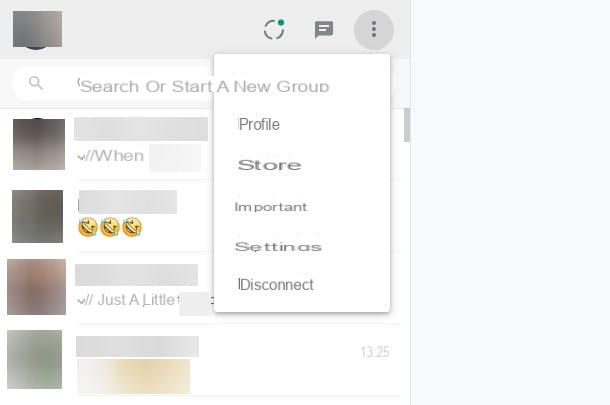
Another problem that arises with the SilverCrest Monsieur Cuisine Connect robot is the absence of Google services. To use their robot in tablet mode and access third-party applications, the people who referred Numerama followed a tutorial. This includes the installation of Google Apps once the ROM has been flashed.
At this level, it's no longer a food processor, it's a colander
Concretely, this means that they are not integrated on the Monsieur Cuisine Connect by default and therefore that the food processor is not certified by Google. It therefore does not benefit from Google Play Protect once out of the box. In other words, not only does the Monsieur Cuisine Connect from SilverCrest not benefit from the security updates deployed on Android for 20 months, but it also does not benefit from a security barrier that would block the installation or the use of a malicious application from the outside. At this level, it's no longer a food processor, it's a colander.
As a reminder, Google Play Protect is Google's home security solution. Integrated directly into Google services, it will regularly scan the applications installed on your device to protect you in the event of a malicious application. Like any antivirus, it will then alert you in case of danger and encourage you to remove malicious software. Without Play Protect, no antivirus.
"We neglect the risk of attack by physical vector"
However, this does not mean that Android is not secure, as Pierre-Olivier Dybman, Android developer (and co-founder of TechnologiesTips) points out: “Each application runs in its own instance of the virtual machine. Impossible for an application to use another (outside the mechanisms that are provided). It is therefore impossible for an application that does not have the permissions to perform an action X to use another application that does have them”. Nevertheless, according to him, one of the main risks in this case would be physical access to the robot and therefore to its USB socket: "Generally speaking, in the world of consumer connected objects, by convention, we neglect the risk of attack by physical vector”.
Limited risks for the general public
However, according to Imran Khan, head of the protection and IoT laboratory at Avira, “There are ways to access hidden permissions and bypass these techniques on devices that are no longer up to date”. This is enough to allow you to bypass the application partitioning system provided you have physical access to the Monsieur Cuisine Connect robot. Concretely, then it would be possible for a spyware to record and listen to any discussion that would take place next to the robot cooker thanks to its microphone. "People who have successfully exploited vulnerabilities could listen to or record the microphone," says Jacques de La Rivière, president of cyberattack detection probe provider GateWatcher.
"A connected object on an outdated Android is often much more secure than a connected object with an in-house OS"
Still, in the majority of cases, it will be very difficult for a pirate to exploit one of the Android flaws present on the robot. This is what Pierre-Olivier Dybman tells us: “There is not zero risk, but there are so few risks and so difficult to exploit that we will never go through it. A connected object on an outdated Android is often much more secure than a connected object with an in-house OS”. For the developer, there would have to be flaws at all levels, on the ROM, on the applications, on access to the device and on access to the network. However, in the vast majority of cases, such a combination of circumstances is quite rare: “physical access would be catastrophic for the security of the device. But from a distance, compromising this device will be very difficult.”
"the seller should communicate on all features, even if they are not activated"
For Avira's Imran Khan, the observation is more severe, but the main lesson to be learned is SilverCrest's responsibility: “the vendor should communicate on all features, even if they are not activated”. According to him, the manufacturer should communicate more about the presence of a microphone and the version of Android. Above all, it should offer an operating system update as soon as possible, at least to correct security flaws.
 Monsieur Cuisine Connect: a hidden microphone on this robot running Android 6 Marshmallow
Monsieur Cuisine Connect: a hidden microphone on this robot running Android 6 Marshmallow

The Thermomix food processor from Vorwerk is the new favorite companion for lazy cooks. Choose your recipe, put your ingredients in the indicated compartments and press the button, the robot takes care of everything!…