WiFi networks have become the norm, but pose a number of security concerns: they can allow an intruder to access your home network, the machines connected to it, and its traffic. A malicious person can carry out their attack from a distance, with complete discretion. However, strengthening the security of your WiFi network is not just, as you will see, just changing the network key. Here are some tips to improve the protection of your network against possible intrusions.
 Summary
Summary- WiFi: limited security, whatever you do
- Password, security...: basic advice
- More advanced tips for securing your WiFi network
- Complicated Methods We Don't Recommend (and Why)
- Comments
WiFi: limited security, whatever you do
The first advice is not to believe that it will be possible for you to make your WiFi network completely impervious to attacks. The technology has several flaws. First, it relies on waves that pass through walls: the signal is therefore accessible all around your home, which is particularly true when you live in a city apartment.
The second problem is that encryption is no longer absolute security. Known and well-documented vulnerabilities (in particular the WPS) allow for example to access wireless networks without even trying to guess the key on some non-updated routers. WEP and WPA ciphers are now very easy to crack. And since last year, the security of WPA2 encryption has also been cracked.
Since then, the WiFi Alliance has announced WPA3 encryption, which should make it possible to regain some time ahead of pirates. But routers, like more generally WPA3 compatible devices, are still rare. And in the end we expect in any case that pirates will end up finding a new parade...
The first way to strengthen the security of your WiFi network is therefore to strengthen the security of what is most at risk of being hacked, namely the security of the devices connected to your network. Hence the relevance, for example, of a firewall directly on your computer rather than relying on that of your router.
Password, security…: basic advice
Let's start with common sense advice that is unfortunately not always respected. If you already know them, skip ahead to more advanced tips, and/or methods we don't recommend.
Choose a strong password for your WiFi network
In general, your WiFi network is managed by your operator's box. This means that in general, your operator has already assigned you a very complex connection key that you don't have to change. Unless your box is in common areas and you want to prevent anyone from connecting with the code pasted on the box label.
Either way, if you do change it, go for something both mnemonic and secure. In this article we give you sound advice for choosing better passwords. One of them is to construct your passwords as phrases (series of pronounceable words) rather than series of numbers, letters and special characters.
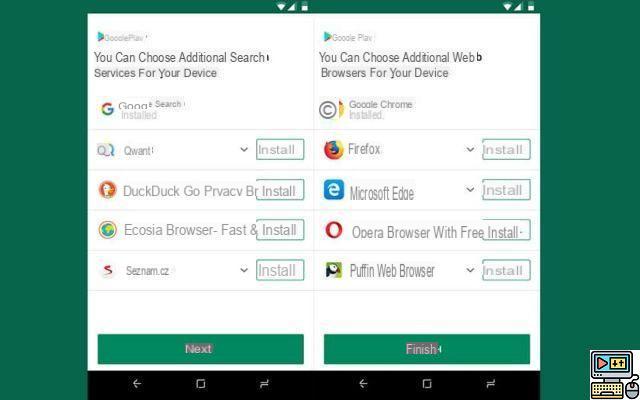
Choose the highest cipher compatible with your devices
In general, all routers offer these encryption methods (the most secure in the list in bold):
- WEP 64 bits
- WEP 128 bits
- WPA PSK (TKIP)
- WPA-PSK (AES)
- WPA2-PSK (TKIP)
- WPA2-PSK (AES)*
- WPA/WPA2-PSK (TKIP+AES)
* the strongest cipher on most routers is this one, not the one just after as many users unfortunately believe…
More recently, some devices also offer this method:
- WPA3
WEP (Wired Equivalent Privacy) is the oldest of the encryption methods – and is now almost as recommended as leaving your network passwordless (whether in its 64 or 128 bit version). It is a method to be avoided in all cases.
WPA (Wi-Fi Protected Access) is a series of standards designed to improve security. WPA I was quickly superseded by WPA2, and more recently, after critical protocol flaws were discovered, the WiFi Alliance released WPA3. The problem is that this latest technology is still slow to democratize.
TKIP is the old encryption method used by the WPA protocol.
BEA is a strong encryption standard used, among others, by the army.
The mode WPA/WPA2-PSK (TKIP+AES) is not, contrary to popular belief, the most secure mode available on your router. It is actually a hybrid mode that mixes the two versions of WPA and encryption protocols (TKIP and AES) for more compatibility. It nevertheless allows hackers to take advantage of the vulnerabilities of the WPA I protocol – knowing that the WPA 2 protocol is also now vulnerable. And also allows to exploit TKIP, a less secure encryption than AES.
That's why if your devices allow it, we recommend that you choose WPA2-PSK (AES) mode on your router. Since WPA3 is still slow to appear.
Change the name of your network SSID
By default, your internet box broadcasts a name that betrays its origin. For example, if you have a Livebox, your default WiFi network name will be something like Livebox-F986. Each operator has its nickname, and this therefore gives an important indication to a potential hacker who will seek to exploit a flaw in your equipment: if it is a Bbox, Livebox, Freebox or SFRbox, all that remains is to test the vulnerabilities of the most recent models.
But why not try to confuse everyone instead? Choose a different name – whether it's something totally unrelated, or something like another operator's box. This won't really improve your security, but it will definitely waste a potential hacker's time.
Keep your router up to date
It goes without saying that if there are faults, the manufacturers tend to correct them, and offer regular updates. However, the update is not always automatic on all models. You must therefore log in to your administration area.
How To: Log Into Your Router's Admin Interface
More advanced tips for securing your WiFi network
Alongside the basic advice, a few actions will allow you to raise the security a few notches to reduce any risk of attack.
Disable WPS
WPS, for Wi-Fi Protected Setup, is a technology launched by the Wi-Fi Alliance to simplify the connection of a device to a Wi-Fi network. press to validate the pairing of a device to the WiFi network, replacing the password. But there are several WPS connection methods. One of them is based on an eight-digit PIN code – factory set, sometimes 12345678 is found on older models.
But other flaws exist on more recent models with other WPS connection modes. For example, an attack on the protocol was demonstrated in 2017 on Livebox 2 and 3 and Neufbox 4, 6 and 6V. The flaw was rather worrying, since the attacker only had to send an empty PIN code to initiate the connection. In short, if you do not use it – many users do not even know the existence of this feature on their router – deactivate it via the management interface of your box.
Hide the SSID
To go further, you can opt for a strategy aimed at making your network as discreet as possible in an environment already saturated with numerous WiFi networks. One of the tips for this is to hide the SSID network name. This means that it will no longer appear in the list of wireless networks on computers, smartphones and tablets.
It is nevertheless possible to discover the presence of a hidden network using specialized tools, but this adds difficulty to penetrate your wireless network since to connect to it, it is absolutely necessary to know the name of the network and the key. Again, this should not be viewed as an actual security measure. This is at best an obstacle that will waste a little time for a hacker.
To connect to your network, you will now have to manually enter its name, security standard and key.
How To: Log Into Your Router's Admin Interface
Reduce the strength of the signal and therefore its range
Unfortunately, not all routers allow this, but one of the best ways to make your network less vulnerable to attacks is to reduce the strength of the WiFi signal. It then becomes much more difficult to connect outside your walls, the connection being weaker.
In the same vein, opt, if your devices are compatible, for a single 5GHz WiFi network (and deactivate the 2.4 GHz network): the higher you go in the radio wave spectrum, the more easily the signal is blocked by walls. We also advise you to deactivate the WiFi network if possible when you leave your home for long periods of time – for example when you go on vacation.
How To: Log Into Your Router's Admin Interface
Take a look at the list of connected clients from time to time
Go from time to time to take a look in the administration pages of your router to consult the list of connected devices. Try to check that all devices are among those allowed. To do this, you can help yourself, among other things, with the MAC address of your devices, which makes it possible to guess the brand of the device. This site allows you to find a lot of information from MAC addresses:
- macvendors.com
Also read: How to check if someone is stealing your WiFi and how to protect yourself
Choose a different login / password for the administration of your router
Imagine that an intruder manages to enter your network without your knowledge and to change the configuration of your router to reduce the risk of being discovered, or to carry out an attack. It is for this reason that it is strongly recommended to change the router's default username and password, even if its management interface is only accessible from your network. If the login/password in question is Admin/Password (it's often that or something like that, alas), change it urgently.
How To: Log Into Your Router's Admin Interface
Complicated Methods We Don't Recommend (and Why)
Besides that, there are methods that we have read elsewhere on the net, and which are to be avoided, because they unnecessarily complicate the use of the WiFi network (and are therefore likely to be quickly abandoned) and /or because they do not really improve the actual security of your WiFi network, in addition to making your connection less stable.
mac address filtering: to try it is to hate it
Often recommended, Mac address filtering should be avoided for two reasons. The first, probably the most important, is that it is possible to manipulate this address, which was initially designed as a kind of electronic watermark. An intruder will therefore be able to brute force find authorized mac addresses and pretend to be a valid device.
The second is that each time you have guests, you will need to retrieve their mac address and put them in the list of authorized devices to connect them to WiFi. We're betting that it won't amuse you for more than two minutes!
Install a VPN on the home router
We have seen in other files on the subject some advising to configure a VPN on your router. We believe this advice is a distortion of another, wise one: to use a VPN when connecting to public WiFi networks. The idea is to encrypt the traffic between your machine and the rest of the net, making man-in-the-middle attacks more difficult.
But at home, we talk about a private network – a place where the risk posed by this kind of attack is very low (especially if you follow the advice above). Also, aside from helping you connect to Netflix US on all your devices in the house, setting up a VPN network on your router (instead of your devices) will add absolutely no security to your WiFi network.
Finally, having tested the thing on several models of routers (notably Netgear with Voxel or DD-WRT firmware…), this tends to make the connection unstable with fairly frequent cuts, which can last several minutes each time. You then risk being one of the most hated people in your household, identified as the one "who always rots the internet connection with his hacks" and that, frankly, believe me, it's not cool (I don't know something!).
Also Read: How To Automatically Switch To The Strongest Wifi On Your Android Device
Do you know any other tips to make your WiFi network more secure? Share your opinion in the comments!