Preliminary information

To find out what are the main techniques used by cybercriminals for hack WhatsApp I must provide you with some preliminary information that can allow you to understand well how the application works and what are the protection systems adopted by the latter.
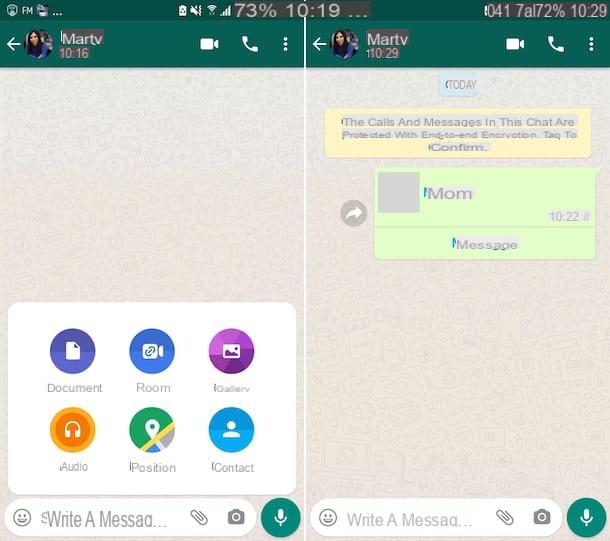
WhatsApp uses a system of end-to-end encryption (from point to point) which allows you to view the content of conversations only to legitimate senders and recipients. Thanks to it, the information is protected with a sort of digital lock, travels in an encrypted manner to the WhatsApp servers and then arrives on the recipient's device, where it is decrypted and therefore readable by the latter.
Everything happens automatically, without users having to do anything, thanks to two cryptographic keys: a public which is shared between users and a private which resides exclusively on each user's smartphone. Another important thing to underline is that the encryption covers not only text messages, but also photos, videos and all other content that can be managed by WhatsApp.
To be more precise, the encryption system used by WhatsApp is called Textsecure, is open source and was developed by the company Open Whisper Systems, which announced its collaboration with the famous messaging service in November 2014. This means that previously WhatsApp did not use the same protection measure. In fact, it used an encryption system based on the RC4 algorithm, which worked only outgoing (from the sender's device to the service's servers) and was much easier to attack.
Some tests carried out by the security company Heise in April 2015 showed that end-to-end encryption had not been adopted simultaneously on all versions of WhatsApp: at the time of the tests it was only present on Android, while on other platforms software was still used the RC4 algorithm, but now the situation has changed and luckily end-to-end encryption is active on all versions of WhatsApp regardless of the operating system installed on the device. If you want more information about it, you can also read my tutorial on how to encrypt WhatsApp.
In light of the above, WhatsApp should now be reasonably secure, end-to-end encryption should prevent attackers from capturing conversations via activities such as sniffing of wireless networks (i.e. monitoring the network to which the reference device is connected, which I told you about in detail in my guide on how to sniff a wireless network), but unfortunately there are some unknowns that need to be taken into account.
First of all, it must be said that WhatsApp is software closed source, so we cannot thoroughly examine its source code and we cannot know if the end-to-end encryption has been implemented flawlessly. Then they exist other techniques, such as those you find reported in this tutorial, less refined than wireless sniffing but no less effective, which allow you to spy on WhatsApp and conversations within the app.
In 2021, for example, there was a bit of controversy because it was discovered that by reporting content in WhatsApp, the messages to be reported are seen in plain text by the staff of the social network, together with the four previous ones (sent to give "a context "to the conversation), but this is quite normal, given that the reports must be evaluated on the merits by the service managers and are sent voluntarily by users (it would not make sense to send a message for the evaluation by the WhatsApp staff unreadable!).
How to hack WhatsApp
At this point, I would say that we are there: we can finally get to the heart of the guide and go and find out, therefore, what are the techniques most common among the bad guys to hack WhatsApp. You can find them listed below.
Cloning of the MAC address

A technique for hacking WhatsApp that is very popular among cybercriminals is that which provides the MAC address cloning, or rather the installation of a "cloned" copy of the app. What is meant by a "cloned" copy? I'll explain it to you right away.
By disguising the MAC address of your smartphone and activating WhatsApp with your phone number, an attacker could use the messaging service on his smartphone, tricking the app's verification systems and accessing your account undisturbed.
Il MAC address, in fact, it is a numerical code that uniquely identifies all devices capable of connecting to the Internet and WhatsApp uses it, together with the telephone number, to verify the identity of users.
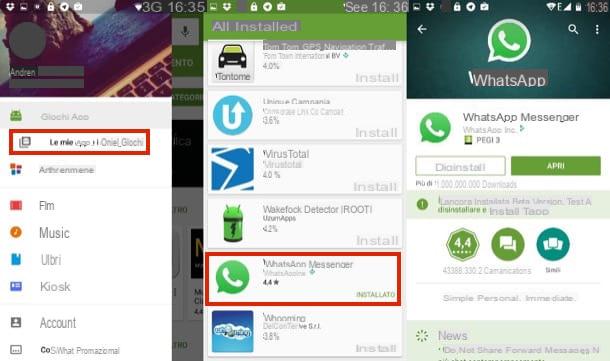
Now, if someone with medium-high computer knowledge manages to steal your smartphone and discover the MAC address of the device (information freely accessible from the menu with the information of the operating system), they can use applications to disguise the MAC address of their smartphone ( ex. BusyBox e Mac address ghost for Android or SpoofMAC for iPhone, which I told you about in my guide on how to clone WhatsApp) and make it look the same as yours.
At this point, the "spy" on duty can install a copy of WhatsApp on his mobile phone, activate it using your phone number (so by sending the SMS with the verification code to your device) and access the service by pretending you, thereby gaining full access to your conversations.
In itself, therefore, the cloning of the MAC address is not a very complex operation, but to complete it you must obtain physical access to the victim's smartphone and you must also have a lot of time at your disposal.
What if someone, with more modest computer skills, tried to activate a new copy of WhatsApp with your number? The answer is soon given: without preventive cloning of the MAC address it would prove to be a rather useless operation. WhatsApp, in fact, allows you to associate each phone number with only one smartphone at a time. This means that the legitimate owner of the account could regain full possession of their identity simply by reactivating WhatsApp on their smartphone. The spy's phone would automatically lose access.
Spy app

Another danger to which we must be very careful are the so-called spy app, that is applications, often invisible to the user's eye, capable of hacking WhatsApp by recording the messages composed on the keyboard, capturing screenshots of the phone screen and sending other information to people remotely.
There are so many applications of this kind: some of a more natural nature professional and paid, designed with the clear purpose of spying on users and others often free, which officially serve to carry out activities parental control or to monitor the phone in case of loss / theft but which configured properly can become all-round spying tools. Fortunately, however, these are not apps for everyone and, moreover, they are very expensive and can only be used on devices that have been rooted or jailbroken.
Among the most advanced and popular spy applications at the moment I point out iKeyMonitor, which is compatible with both Android and iPhone and allows you to spy on all activities: the apps used, the messages exchanged, the texts typed on the phone keypad, the calls and much more.
Among the parental control apps, however, I point out Qustodio, which is usable on both Android and iOS, as well as Screen Time, also available for both Android and iOS, which allow you to monitor the applications run on the phone and limit their use, even if they do not allow direct tracking of messages exchanged within WhatsApp.
WhatsApp Web / Desktop

You know Web WhatsApp? This is an online service that allows you to use WhatsApp from your computer without installing specific software. And of WhatsApp Desktop, have you ever heard of it? It is the client for Windows and macOS of the famous messaging service that is the subject of this guide. I have described both solutions to you in my tutorial on how to use WhatsApp on PC.
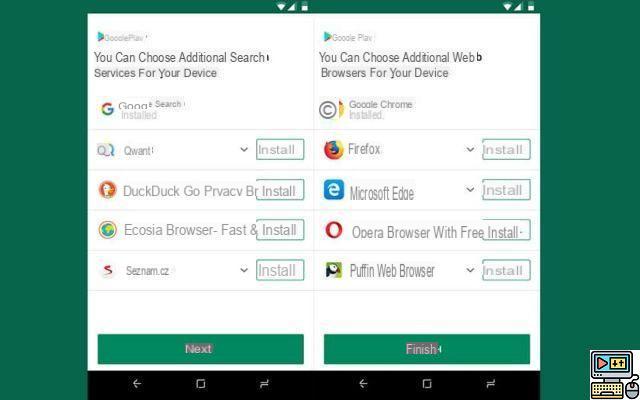
Both WhatsApp Web and Desktop are able to store the user's identity, so after the first login there is no need to authenticate again and it works even if the smartphone is not connected to the same wireless network as the PC (as long as it is connected to any Wi-Fi network, or even to the 3G / 4G / 5G data network) and even when the smartphone is not connected, if the WhatsApp settings have been activated multi-device function (which at the time of writing this tutorial is still in beta, more info here).
From these "clues" you can easily understand that an attacker could steal your phone with any excuse, use it to access WhatsApp Web on his computer (just scan a QR code with the mobile phone camera) and spy on your messages, although to date this technique can no longer be considered 100% valid as WhatsApp sends notifications relating to access and requires biometric identification to activate access.
How to hack WhatsApp without victim phone

In case you were wondering if there is a way to hack WhatsApp without having the victim's phone close at hand, I answer immediately that yes, the thing is feasible, although in this case the term "hacking" is not exactly correct.
You must know, in fact, that there are some services to monitor access to WhatsApp, usable in the form of an app or from the browser, which offer the possibility of obtaining the data in question by typing the telephone number of the person of your interest.
They do not require physical access to the victim's smartphone and you cannot defend against their action, as WhatsApp access times are public data after all, but fortunately they do not act in any other way.
In most cases, using such solutions is totally free, but some advanced features, such as exporting the data obtained, are only available for a fee. Furthermore, it must be taken into account that from time to time services of this type stop working properly or even completely.
How not to get hacked WhatsApp

As I had anticipated at the beginning of the guide, it seems only right to indicate you too how to avoid that an attacker can hack your WhatsApp account by putting into practice the techniques I have described to you in the previous lines. Below, therefore, you will find a whole series of useful tips.
- Update WhatsApp - by always downloading the latest updates available for the WhatsApp app, you can prevent attackers from using any flaws that they may find in the app code. For more details about it, you can read my guide on how to update WhatsApp on iPhone.
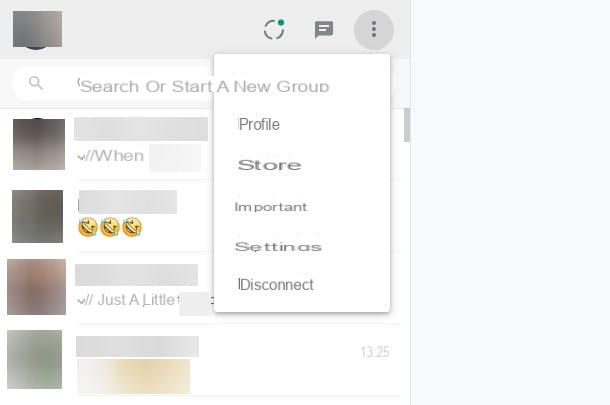
- Disconnect the devices from WhatsApp - if you are concerned that someone is using your WhatsApp account without your knowledge, to resolve disconnect all devices currently active with the service. To do this, you just need to intervene from the app settings, as I explained to you in detail in my guide on how to disconnect WhatsApp Web.
- Enable blocking on WhatsApp - you should know that WhatsApp provides its users with a function that allows you to block access to the application by face or fingerprint, which allows you to prevent access to your conversations to those who are not authorized. To understand how to enable this feature, read my guide on how to put the block on WhatsApp.
- Set a secure PIN - if you use a sufficiently secure PIN on your mobile phone, you can prevent malicious people from accessing your phone and, consequently, also WhatsApp. Most devices also allow you to configure unlocking by setting the use of your fingerprint and face. For more details, see my article on how to lock the screen.
- Disable SMS display on lock screen - by cloning the MAC address of the smartphone, an attacker can activate WhatsApp on his phone using his number. To do this, however, he must be able to read the verification code provided by SMS on your mobile phone. Therefore, by disabling the display of SMS on the lock screen you can prevent situations of this type from occurring. To understand how to proceed, read my post on how not to show messages on the lock screen.
- Don't use public Wi-Fi networks - end-to-end encryption should not make sniffing of wireless networks possible, but for greater security I suggest you avoid connecting your mobile phone to public Wi-Fi networks and / or networks that do not have adequate security. Instead, use your SIM's 3G / 4G / 5G network. Alternatively, you can a service VPN (virtual private network) on your smartphone. Thanks to services of this type, such as NordVPN (which I told you about in depth here) and Surfshark (which I told you about here), you will be able to encrypt all the data on your connection making them inaccessible to the outside, overcome regional blocks, censorship and even access the foreign catalogs of streaming services. All at fairly low prices.
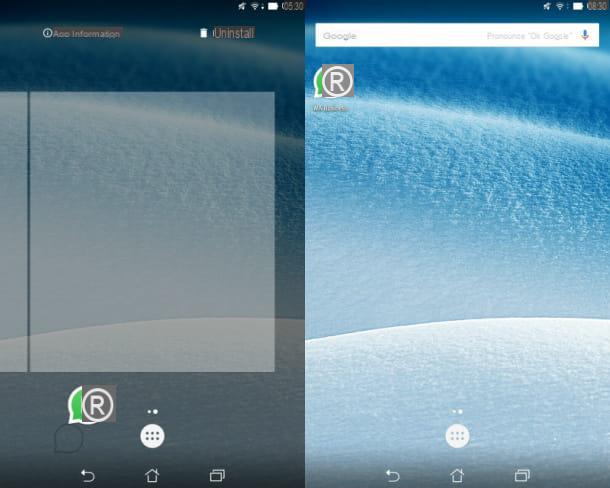
- Check for spy apps - if you think there may be some spy apps on your mobile, access the list of applications installed on them to check this and, of course, remove them as soon as possible. For more information, read my post on how to delete spy software from your mobile.
- Reactivate the disabled account - if someone has enabled WhatsApp on another device with your phone number, you will no longer be able to use it on your smartphone. If you find yourself in such a situation, contact WhatsApp support to report the matter. To find out more, read my guide on how to contact WhatsApp.