Spy on WhatsApp remotely by sniffing wireless networks

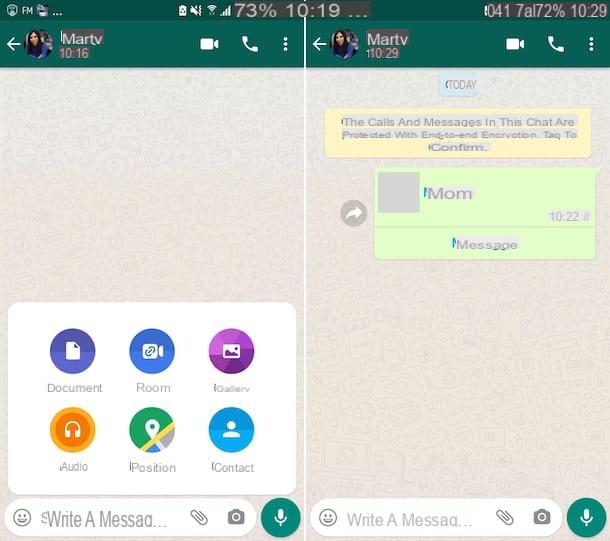
Wireless sniffing is a well known technique. It consists in capturing all the data passing over a wireless network using easy-to-find software such as the very famous Wireshark (which I also told you about in my post on how to sniff a wireless network). This is one of the most feared dangers by WhatsApp users, but in reality its danger has been almost completely canceled by the adoption of the end-to-end encryption by the well-known app now owned by Facebook.
If you've never heard of it, end-to-end encryption is a system that encrypts computer communications using a system consisting of two keys: one public and one private. The public key is shared with your interlocutor, while the private key resides only on each user's smartphone. This means that messages travel in encrypted form to the WhatsApp servers and no one, other than the legitimate senders and recipients (ie those who are in possession of the keys to decrypt them), can read the contents. Even if they are captured by sniffing wireless networks, they would be unreadable.
A study carried out in April 2015 by some German researchers had shown that not all versions of WhatsApp used end-to-end encryption (only the Android one used it), but luckily things have changed since then. End-to-end encryption is now active on all software platforms (Android, iOS, Windows Phone etc.) and protects all communications, including calls. If you want to know more, feel free to check out my tutorial on how to encrypt WhatsApp.
The only unknown factor to be taken into account is represented by the fact that WhatsApp is a closed source application, its source code cannot be thoroughly analyzed, and therefore we cannot know if the end-to-end encryption has been implemented properly. Some mistake may have been made that could undermine the functioning of the system or, again, the encryption could be intentionally disabled in some circumstances or countries for reasons unknown to us.
In short, we must trust the developers of WhatsApp and TextSecure (those who created the encryption system used by WhatsApp but we must never let our guard down. never use public Wi-Fi networks (which is known to be the favorite hunting ground for cybercriminals) and not to use WhatsApp to communicate highly confidential information.
That said, it's always a good idea to use one VPN. If you have never heard of it, it is a system that allows you to connect to the Internet via a virtual private network and thus encrypt your navigation data, making them invisible to malicious people and providers. It also allows you to disguise your geographic location and overcome online censorship. Among the cheapest and most functional VPNs you can try, there are NordVPN (which I told you about in depth here) and Surfshark that work on all devices and operating systems and have very low prices.
How to protect yourself
If you are "paranoid" and want to minimize the risk that someone may "sniff" your communications remotely, I'm sorry, but you have to abandon WhatsApp and go to another messaging application; an open source application that uses an end-to-end encryption system of proven reliability. A few examples? Signal for Android and iOS which is developed by the same creators of the TextSecure technology used by WhatsApp and has a reliable "sponsor": Edward Snowden, the main architect of the datagate following which many confidential documents of the US government have been published1.
Spy on WhatsApp remotely via identity theft

Now let's move on to some techniques that potentially allow you to spy on WhatsApp remotely but they require physical access to the victim's smartphone (perhaps for a short time, but they require it).
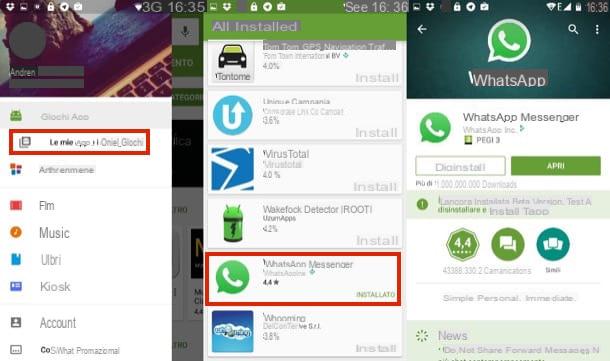
The first technique of this type - the easiest to implement - is the identity theft via WhatsApp Web or WhatsApp for PC. As I also explained to you in my tutorial on How to use WhatsApp on PC, to use WhatsApp on your computer just connect to the official website of the service or download the official WhatsApp client for Windows / macOS and frame a QR code with the smartphone camera.
Once this is done, if you leave the check mark next to the item active Stay connected, you get permission to access the messages on your smartphone at any time. As long as your phone is switched on and connected to the Internet, not necessarily the same wireless network as your computer (3G / LTE data network is fine too).
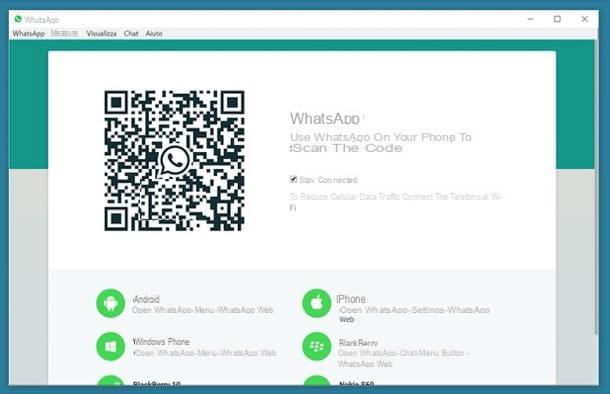
These two factors could push an attacker to ask you for a loan of your smartphone for a few minutes (perhaps with the excuse of having to make an urgent call), use it to access WhatsApp Web or the WhatsApp client for PC and thus obtain continuous access to yours. conversations.
However, it must be specified that, to date, this solution could be difficult to implement. In fact, if the device owner has set biometric recognition protections, such as unlocking the device via facial recognition or fingerprint, access to WhatsApp Web / Desktop does not take place until it is confirmed with one of these systems.
Another technique related to identity theft, which is much more difficult to practice but which you must pay attention to, is the MAC address cloning. As I also explained to you in my post on how to clone WhatsApp, there are some applications that allow you to disguise the MAC address (a 12-digit code that uniquely identifies all devices capable of connecting to the Internet) and deceive verification systems. of WhatsApp. Quite famous examples are SpoofMAC for iPhone e BusyBox and Mac Address Ghost per Android, but there are other apps of this kind as well.
Now, if an attacker manages to get hold of your smartphone, set his phone to have the same MAC address as yours (at least in appearance) and install a copy of WhatsApp by activating it with your number, he can get free access to your conversations bypassing standard service restrictions (which normally prevent the application from being used on more than one smartphone at the same time).
How to protect yourself
To defend yourself against these threats, considering the fact that they all require physical access to your phone, you need to put into practice some evergreen common sense advice.
- Do not lend your smartphone to strangers and do not leave it unattended for too long.
- Set a Secure PIN to prevent someone from unlocking your phone and using it to access WhatsApp Web or to check its MAC address. If you don't know how to set a PIN, here are the instructions for Android and iPhone.
- Android - go to the menu Settings> Security> Screen Lock and select the item PIN from the screen that opens. If your smartphone has a fingerprint sensor, you can also set fingerprint unlock by going to Fingerprint. Avoid the sequence as it is quite easy to guess for those who observe the unlocking of the smartphone from the outside.
- iPhone - go to the menu Settings> Touch ID and Passcode I will select the voice Change codice. If you have an iPhone model equipped with Touch ID, you can set the unlock via the fingerprint sensor by pressing on the voice Add a footprint.

- Prevent SMS from being displayed on the lock screen, so that malicious people cannot see the SMS with the WhatsApp activation code. If you don't know how to do it, here are the instructions for Android and iPhone.
- Android - go to the menu Settings> Security> Screen Lock, select the voice PIN and after setting the code choose to hide only sensitive content.
- iPhone - go to the menu Settings> Notifications> Messages and remove the tick from the option Show in Lock Screen.
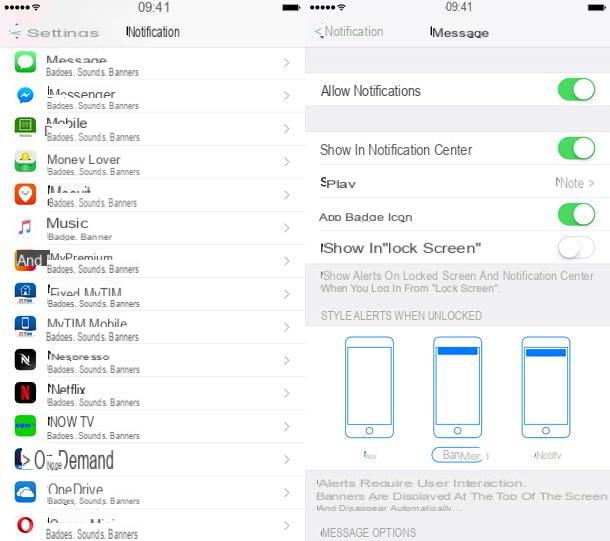
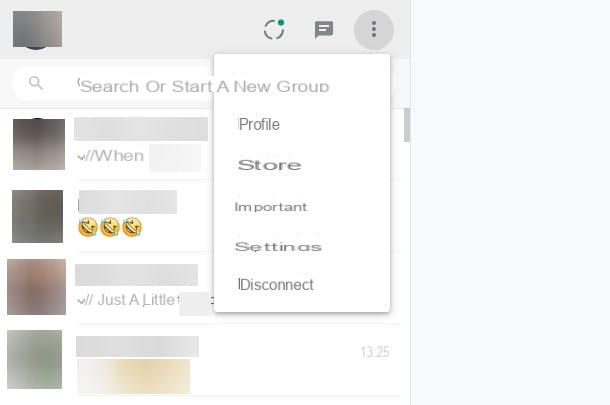
As for WhatsApp Web, you can protect yourself from spying by going to the application settings and revoking access to all currently active WhatsApp Web sessions.
To be more precise, you need to go to the menu (…)> WhatsApp Web (Android) or Settings> WhatsApp Web / Desktop (iPhone) of WhatsApp and press the button Log out of all computers. In this way, any “spies” connected to your account will no longer be able to access the service, as they will be asked to re-scan the QR code with the smartphone camera.
Spy on WhatsApp remotely with an application

Another risk you need to pay close attention to is the one related to spy-applications. As I also explained to you in my posts on applications to spy on mobile phones and on how to spy on Android smartphones, there are applications that are invisible to the user's eyes and allow you to spy on all activities carried out on the smartphone: from texts typed on the keyboard to sites visited. Spy applications can be divided into three broad categories.
- The parental control apps - these are applications designed to control smartphones used by minors. They are very easy to install and use, they can often be used for free (at least for a certain period of time) and allow both to monitor the device remotely and to limit / block the operation of certain apps. Fortunately, they don't hide as well as professional spy apps and are often unable to capture texts typed on the smartphone keyboard. Among the most famous apps of this type there are Qustodio (Android / iOS) and Screen Time (Android / iOS).
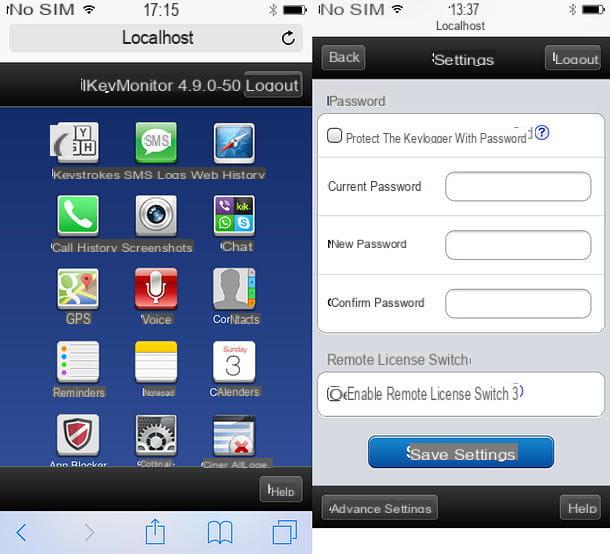
- Spy apps - the real spy applications, those that are able to really track everything and that are perfectly invisible to the user's eyes. Fortunately, they are not for everyone as they are not free (if you exclude a few days of free trial) and they are not very easy to configure. Among the most famous apps of this type I point out iKeyMonitor which is available for both Android and iOS and costs $ 22,49 / month (after 3 days of free trial).
- The apps to monitor access to WhatsApp - even if they cannot be properly defined as spy apps, there are applications that allow you to monitor access to WhatsApp by other users simply by typing their mobile number (therefore without installing anything on the “victim ”'s smartphone). They only allow you to know the times in which a user connects to WhatsApp, they do not spy on messages, but they still represent a discrete bore from the point of view of privacy (also because practically nothing can be done to protect themselves).
For more information on applications to spy on WhatsApp and how they work, read the post I dedicated to this kind of software. You will find several interesting information in it.
How to protect yourself
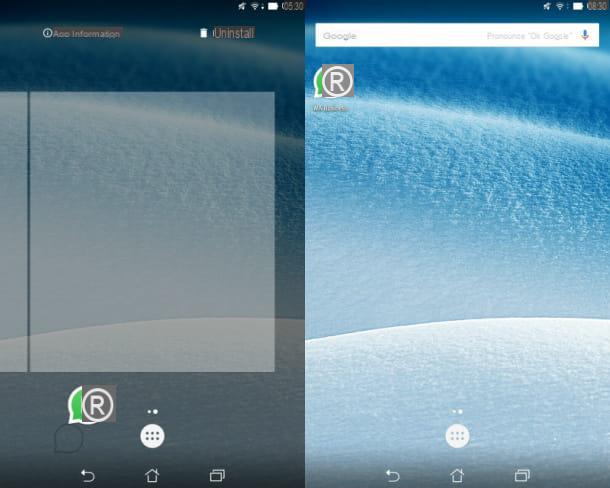
If you suspect that someone has installed a spy app on your phone (another operation that requires physical access to the device), go to the app management menu and check if there are any suspicious names in it.
If you have a smartphone Android, go to the menu Impostazioni> App and check if in the list of applications installed on your device there is any that you think may be a spy app. Next, go to the menu Settings> Security> Device administrators and check if among the apps that have administrator permissions (therefore the apps that can control the phone at 360 degrees) there are apps of dubious origin. Again, if you have rooted your phone, open the application SuperSU / SuperUser and check if among the apps that have root permissions there are some that you have not authorized yourself. In case you find any suspicious apps, disable them and uninstall them.

If you use a iPhone, go to the menu Settings> General> Device and iCloud Space and presses on the voice Manage space contained in the box Device space to get a list of all the apps installed on the device. Then go to the menu Settings> Profile and Device Management and find out if among the applications that have installed custom profiles there are some suspicious ones (the apps that install custom profiles are the ones that have the most control over iOS). If you have jailbroken your iPhone, try opening it as well Cydia and to check the list of packages installed on the phone (many spy apps only work with jailbreak and therefore must be installed via Cydia).
Finally, regardless of the operating system installed on your smartphone, try to open the browser and connect to the addresses localhost: 8888 e localhost: 4444 and try to type the code *12345 in the phone number dialing screen. The codes in question are the codes used by some known spy app to reveal themselves and show their administration panel (if by typing them, you see a menu appear, it means that someone has installed a spy app on your phone).
If you do not notice anything strange but still suspect that someone is spying on you (as already mentioned, these apps have the ability to hide and hardly appear in the clear in the system menus), I'm sorry but the only solution you have at your disposal to get rid of it is format the phone memory. For more information on this procedure, consult my guides on how to reset Android and how to reset iPhone, you will find everything explained there.
Caution: spying on another person's conversations is a crime punishable by law. This post was written for illustrative purposes only, therefore I do not take any responsibility for the use made of the information contained in it.
- Here is the tweet in which Snowden confirms that he is using Signal for his online communications. ↩︎