If you are using a computer shared with other people or if you suspect that an outsider (colleague or family member) has access to our computer without permission, you can certainly spy on his business in a precise way and to know what it does in our absence, so as to be aware of it at the right moment.
If you are using a computer shared with other people or if you suspect that an outsider (colleague or family member) has access to our computer without permission, you can certainly spy on his business in a precise way and to know what it does in our absence, so as to be aware of it at the right moment.Furthermore, at a more advanced level, when two or more people work with their personal computers, at the same desk or even at home or in the same office, they most likely connect to the same router, using the same internet connection. This means that the PCs are networked and see each other.
In this guide we will show you all the tools and procedures for spy on a PC and know exactly what it does and what has been seen or done in our absence; we recommend that you use these methods only to protect our PCs and not to spy on other people's computers (as it is a criminal offense).
How to spy on our PC while we are away
There are various methods we can use to spy on our personal computer while away, so that we know exactly what has been done and find out who has used it or who has researched using our accounts or our Internet browser.Keylogger
One of the most effective methods to spy on our computer involves the activation of a keylogger, to be left active during our absence and to be deactivated as soon as we return to the station. The keylogger records all the keys pressed on the keyboard, so as to provide us with the phrases, words and texts searched on the Internet or on other apps (including any attempts to break the password): if no one has used our computer, the keylogger should be " clean "on our return. Keylogger programs">
Keylogger programs">There are several free keylogger programs available, all seen and reviewed in our AI guides Keylogger programs for Windows e How to install a Keylogger to spy on a PC secretly.
Control programs open and displayed on the screen
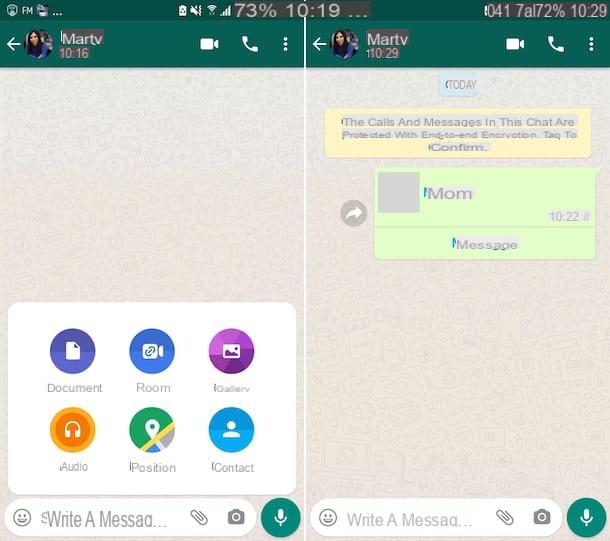
Next to the keylogger we can monitor the computer during our absence using two free programs such as Hooker and Spy Monitor Screen Recorder.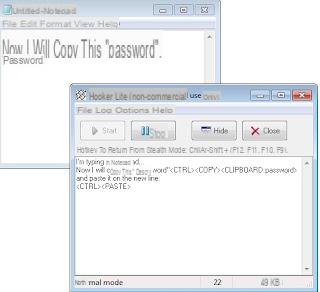
With the first program we will be able to create an advanced keylogger that will show us all the programs open in our absence and all the keys pressed, while the second program is designed to take periodic screenshots of what passes on the screen (programs, videos, Internet etc. ).
By combining the two programs we will be able to discover in a short time everything that has been done on the PC in our absence and collect valuable information about the person who used it.
Record with the webcam
But the most striking evidence is certainly a photo of the alleged "spy", so as to immediately discover who used the computer while we were absent. For this purpose we recommend using WebCamImageSave.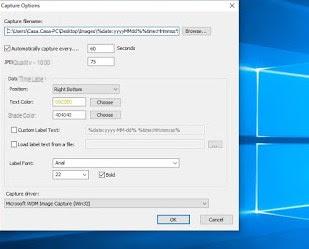
By properly configuring this program at each unlocking or at each restart of the computer during our absence, a photo of the webcam will follow, so that the spy is immediately unmasked! To make the most of this program, we recommend that you read our guide How to activate the webcam when the PC is turned on automatically.
Other useful programs to spy on the PC
The programs seen so far should be sufficient to carefully monitor everything that happens on the computer in our absence; if we are looking for other valid solutions, we advise you to read those below:- A new program to see how your computer is used and also to monitor other PCs on the network is SurveilStar Activity Monitor. This software must be installed on the PC to be controlled which can be that of a family member at home or a work colleague. It is used to check how the internet is being used by another computer, monitor it and, if necessary, also block some sites so that they cannot be viewed. This program works via the sniffing driver for Windows Winpap and, as it is manually installed on the monitored computer, it captures all information on visited sites, e-mails and file transfers. SurveliStar Activity Monitor is free for personal use and is a regular program, which is not blocked by antivirus.
- Everlasting to spy on those who use their pc and record everything they do, you can use Blackbox Security that I had described in a previous article on how check other computers on the network. The program always remains to be manually installed on the PC to be spied or checked, but it does not show up, it remains hidden, it is not caught by antivirus and is able to send the recordings via email. Same type of program is Spy Screen quoted in the post about how spy on and log the activities of a computer. An idea to transfer these programs to control target PCs, without using USB sticks, are online hard drives such as Dropbox or, better still, as Box.net which can be used without installing client, therefore without leaving traces.
- iSpy instead it is one of those programs for automatically record from microphone and webcamIn this case we pass to an advanced level of control because we want to record the audio of what is said in a room and also the video of what happens. After configuring the program, with absolute ease, you can go away and let it record all the movements recorded by the webcam. Programs like iSpy or even Yawcam they only record when motion is detected and iSpy also allows you to manage and view recorded videos from other computers.
- Described in another article, Spyrix it's a program to spy on the computer by recording images and keystrokes during its use.
Conclusions
The tools above provide a complete package for monitoring your PC. You can find out what has been typed, which sites have been visited, which files have been downloaded and which emails have been sent. You can also see what is happening in front of your computer remotely via the webcam (even if, on those integrated in the monitors, the light always turns on).If we are looking for something simpler to control what our underage children do on a PC, smartphone or tablet, we recommend that you use specific parental control programs, such as those seen in our guides. Parental Controls and Parental Controls on PC and Internet: 5 Ways to Keep Kids Safe e How to limit the use of smartphones and tablets to minors.
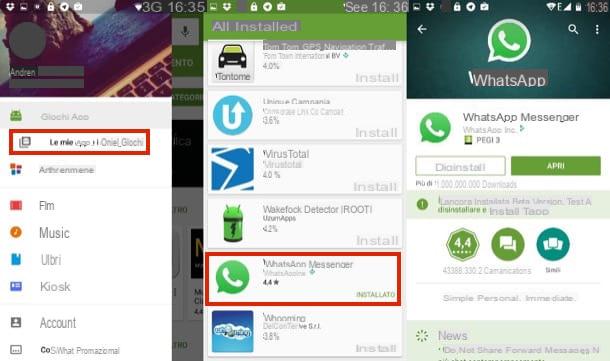
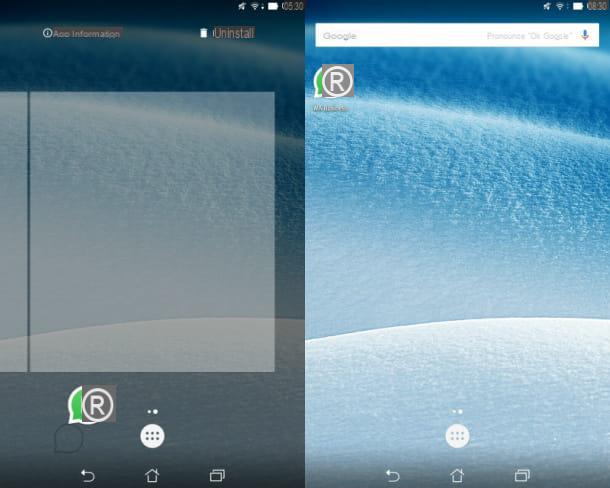
If, on the other hand, we want to spy on an Android device or an iPhone, we refer you to reading our guides Check / spy on another's phone (Android) e Best apps to spy on mobile phones (Android and iPhone).
Spy on a PC and see how the computer is being used by others