What is a Penetration Test
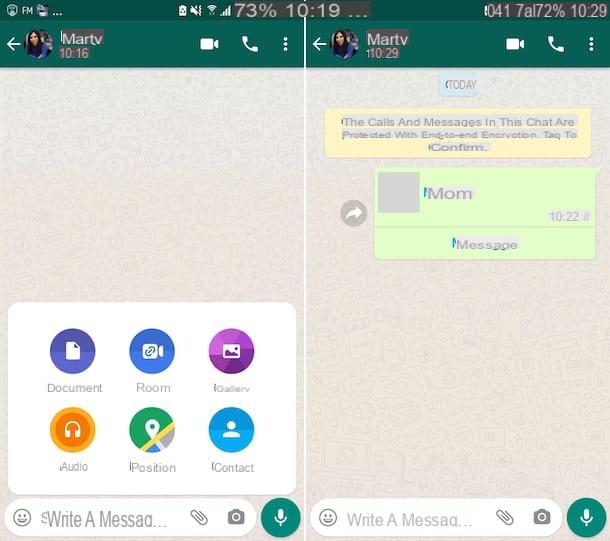
Penetration Test, also called pen test or ethical hacking, is the practice of testing a computer network for identify the presence of any vulnerabilities that a hacker could use to steal data.
This procedure can be automated with software applications or performed manually.
Before the test, information about the target and the identification of possible entry points are collected.
Then an attempt is made to break into the site or network and the results are analyzed.
This way the company gets one exact risk assessment and knows the real level of security of its computer system, to which the entire fleet is connected.
In many cases, penetration tests are used to test for:
1. Privacy policy of an organization and its adherence to the GDPR
2. Security of employees and their data
3. Ability of the organization to identify vulnerabilities and respond to security incidents.
If you manage important data and want to make sure it is safe contact and choose to protect your business by web criminals.
What is it for and when to do it
The Penetration Test makes your company's security system more solid and reliable.
I advantages of the pen test are:
1. Identification of security holes to prevent a hacker attack
2. Identification of vulnerabilities in a network or computer program
3. Gathering of information to eliminate vulnerabilities
4. Creation of a control mechanism for attacks
Before launching any system or software on the market, every company has the obligation, not only moral, to submit it to the Penetration Test and verify its reliability.
What is a vulnerability assessment
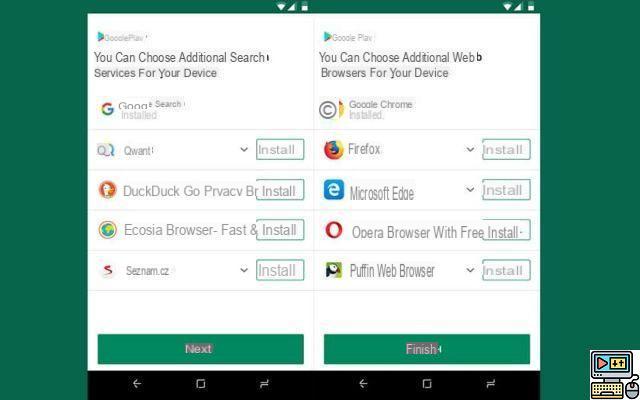
The other option you could choose is the Vulnerabity Assessment.
Basically it is about estimate the cost of information loss based on the impact of a potential attack and the vulnerability of the system to a specific cyber threat.
The company then receives the test results and risk background, information necessary to understand the threats to its environment and react appropriately.
I fields of application of the Vulnerability Assessment cover various sectors, including:
1. IT systems
2. Energy and Utility
3. Transportation
4. Communication Networks
The loss due to the hacker attack can vary, in severity, depending on the system being analyzed.
What is it for and when to use it
Regardless of the size of your organization, you can benefit from a Vulnerability Assessment especially if your company has already undergone it cyber attacks of any size.
Because security vulnerabilities can allow hackers to gain access to IT systems and applications, it is essential for companies to identify and correct weaknesses before they can be exploited by malicious people.
This process gives your business organization a better understanding of assets, security flaws, and overall risks, reducing the likelihood of a cybercriminal breaching your systems.
Differences between Penetration test and vulnerability assessment
The penetration test is the proactive and systematic approach used by ethical hackers or internal testers to simulate a cyber attack on the corporate IT infrastructure and identify with certainty the presence of exploitable vulnerabilities.
These vulnerabilities can exist in systems, services, applications, misconfigurations, and risky end-user behavior.
Unlike the Penetration Test, the Vulnerability Assessment signals detected vulnerabilities, analyzes security systems, detects weaknesses and recommends appropriate corrective measures, in order to reduce or eliminate the risk altogether.
La second difference between the two tests is the degree of automationWhile a vulnerability assessment can be fully automated, pen tests are a combination of manual and automated techniques based on beta testers' ability to identify problems.
La third difference important between penetration testing and vulnerability assessment is the choice of professionals.
Since a vulnerability assessment involves only automated testing, there is no need to hire highly trained professionals.
Conversely, pen testing requires a high level of proficiency, as it is a manual-intensive process.
This is why it is advisable to contact IT security professionals, such as data experts, and evaluate the opportunity for a penetration test: contact us by email or call the toll-free number 800 211 637 now for a free consultation.
Why Penetration testing and vulnerability assessment are important for the security of the corporate network
The statistics from the Trustwave Global Security Report 2019 are alarming:
1. All web applications are vulnerable to attack.
2. All applications had at least one vulnerability
3. The average number of vulnerabilities detected per application is eleven
4. Compared to 2018, the number of reported vulnerabilities is increasing worryingly.
This is largely due to the large increase in the number of people using web applications and the number of them on the market.
Now, the close it's very simple: if you really want to protect your company, your employees and your end customers, the first fundamental step is to secure your computer network.
And you can only do it if you have professionals in the sector as a date to assist you.