REvil ransomware is now able to go through Windows 10 safe mode to automatically change the account password. In this way, it gains easier access to victim's files to encrypt them and then can demand ransom money in exchange for data recovery.

Last March, cybersecurity researchers discovered that a ransomware named REvil restarts its victim's PC in safe mode to encrypt their personal files. To do this, it uses the argument — smode in the Windows 10 Command Prompt. Once the process is complete, it gains access to the files which it can then encrypt before demanding a ransom from the user. Nevertheless, the operation required until now that the latter performs the restart itself for the encryption to take place.
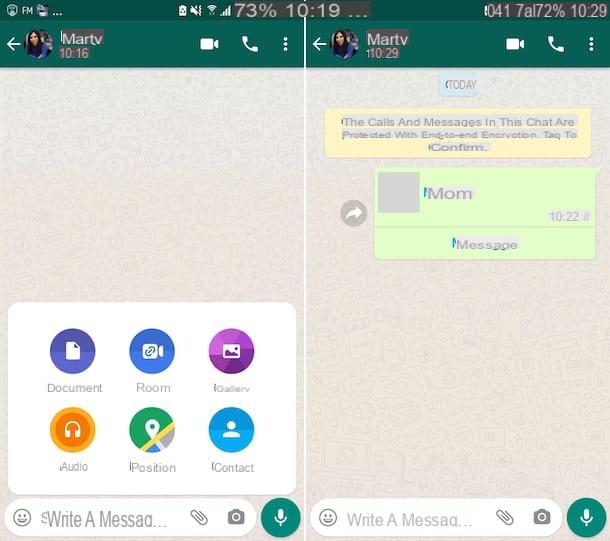
Things have now changed. The malware has indeed acquired two disturbing new features, as reported by researcher R3MRUM. First, REvil changes session password without the victim realizing it. Then, to avoid arousing suspicion, it restarts the PC itself in safe mode to finally start data encryption automatically. Specifically, it configures Windows 10 for the operating system to restart in safe mode.
Related: Windows 10 — How to Remove All Malware for Free with Microsoft Safety Scanner
REvil ransomware evolves and becomes more dangerous
Once installed, REvil changes the user password to " DTrump4ever », before configuring the corresponding registry so that Windows recognizes it as the real identifier. It is possible that another password may be entered in the registry. However, two versions of the malware posted on the VirusTotal database use "DTrump4ever".
It is very likely that this addition has the function of go unnoticed by antivirus and various monitoring programs, just like the Snatch malware does. Moreover, it can in this way disable the recovery applications, as well as the cloud servers in order to increase its chances of encrypting the files.
If the victims do not pay the demanded ransom, they expose themselves to the risk of a DDoS attack on his email address and that of his professional collaborators. Unfortunately, even if it complies with the demands of cybercriminals, they have no certainty of ever getting their hands on their encrypted data. The Ryuk malware is known for deleting stolen files once the ransom is paid.