Comment (3)
Comment (3)
The amount of time between copying a file from one app on your iPhone and pasting it into another has two developers worried.
While Larry Tesler, the inventor of Copy and Paste, passed away last week, the feature that made him famous is now used on a wide variety of electronic devices, starting with smartphones. A gesture that has become so commonplace that it is difficult to imagine that it could give access to sensitive information on your terminal. However, developers Tommy Mysk and Talal Haj Bakry discovered that data copied from an iPhone or iPad could be intercepted by other applications.
The clipboard in the dock
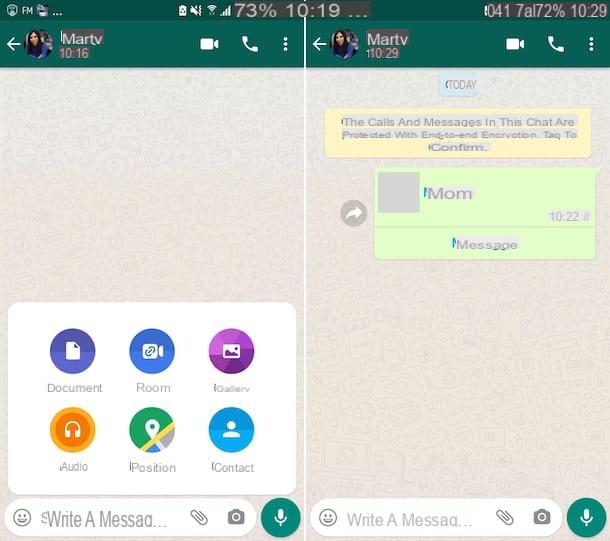
This discovery concerns a rather particular case. Developers found that iOS gives the app running in the foreground access to your iPhone's clipboard, which can be described as volatile memory for recently copied items (pictured , text, password, phone number or link).
After copying content from a first application, Apple presumes that the user opens a second to paste this content into it, causing the process to end. But if the user is distracted, or launches other programs in the meantime, the copied elements can pass through all these applications if they behave maliciously. The developers even suggest that an app would be able to rewrite the data accessible in this Clipboard.
A test app to validate the theory
To test their theory, Mysk and Bakry have developed an application called Klipboard Spy, which clearly shows the information captured when copying a file. In the case of a photograph, for example, the application can retrieve metadata, including the date and time of the shot, but also the GPS coordinates of where the image was captured. On iPad, the widgets visible from the Today View – and which are by definition always active – also raise questions, since they would potentially be able to permanently intercept data passing through the Clipboard.
“A malicious application could detect the presence of an IBAN banking information in the Clipboard and replace it with another IBAN, hoping that the user makes a bank transfer to this IBAN, explain the developers. The malicious scenarios are countless.”
Should we worry?
While these scenarios are countless, as the developers point out, they seem fairly unlikely to occur. In addition to the limited probability that an application behaves maliciously, one would have to rely both on the distraction of the user and on the chance of the data that he copies.
Tommy Mysk and Talal Haj Bakry indicate that they submitted their article and the source code to Apple on January 2, 2020. On February 6, the Californian company replied that it did not see a vulnerability there. Among the solutions recommended by Mysk and Bakry is the addition of a clipboard access permission for each application installed on an iPhone or iPad. But this time it would be necessary to count on the vigilance of the users...