Preliminary information

Before getting to the heart of the guide, going to illustrate how to spy on whatsapp conversations without victim phone, it is my duty to provide you with some preliminary information in this regard, so as to allow you to have a clear idea of the matter.
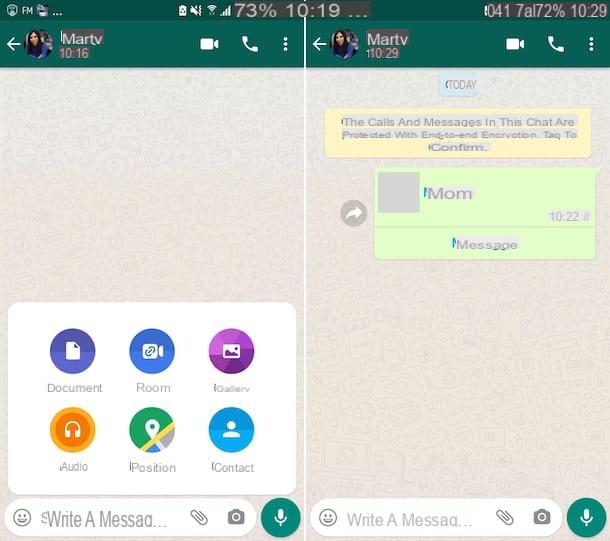
We start from the fundamental assumption that WhatsApp is a sufficiently secure service thanks to the use of the system end-to-end encryption named Textsecure, consequently capture the messages that travel on its servers through Sniffing (a technique that consists in capturing the data that passes over a wireless network using special software, which I told you about in detail in my guide on the subject) seems rather complicated.
End-to-end encryption works with a pair of keys - there is one private key, which resides on the user's smartphone and allows you to decrypt messages received from the outside and there is one public key, which is shared with the interlocutor and is used by the latter to encrypt messages delivered to the other account and vice versa.
The WhatsApp servers act as intermediaries between the two keys, which receive encrypted messages and deliver them to the recipient's device. Everything happens in real time and without the user having to do anything. For more information on this, you can consult my guide on how to encrypt WhatsApp.
However, being WhatsApp a software closed source, so it is not possible to analyze the code thoroughly, unfortunately it is not possible to know with certainty how the messages are actually managed.
Still on the subject of end-to-end encryption, if you don't know it, I inform you that it was introduced on WhatsApp starting from November 2014, thanks to a collaboration between the team of the famous app and the developers of Open Whisper Systems.
However, some tests, such as the one carried out by Heise in April 2015, showed that end-to-end encryption was only used on the Android version of WhatsApp. In all other cases, an encryption system based on the RC4 algorithm continued to be used, functioning only on output and considered no longer secure. To date, the situation has totally changed, as end-to-end encryption has been made available for all platforms on which WhatsApp can be used and covers all kinds of content.
Despite everything, there are other techniques that criminals can try to adopt to spy on WhatsApp, even if they are much more difficult to use and which, as I told you at the beginning of the guide, require a first direct contact with the victim's mobile phone.
How to spy on WhatsApp conversations without victim phone
Having made the necessary clarifications above, I would say that we can get to the point and, therefore, find out how to spy on WhatsApp conversations without the victim's phone. Find indicated below what are the main tactics exploited by the bad guys.
Furto d'identità

Among the most popular techniques for spying on WhatsApp conversations without the victim's phone, or rather without having to constantly have the cell phone of the one or the one you intend to spy on, there is undoubtedly the identity theft.
This is the technique by which the attacker on duty can "deceive" WhatsApp by pretending to be another person and access, without permission, the conversations of the latter. To date, the system for implementing identity theft is only one: the MAC address cloning.
Don't you know what I'm talking about? No problem, I'll explain it to you immediately. The MAC address is a 12-digit code that uniquely identifies all devices capable of connecting to the Internet. It is also used by WhatsApp to verify the identity of users (together with the phone number), but with special applications it is possible to disguise it and deceive the application.
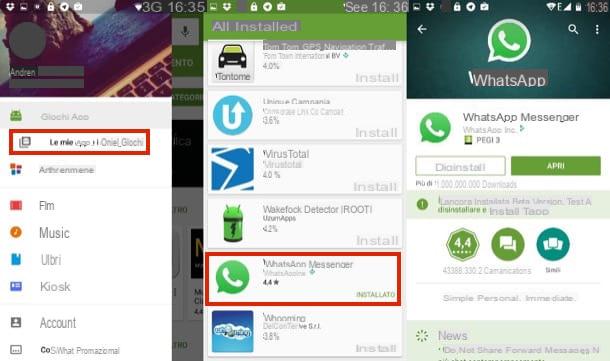
So, if an attacker installs some of these apps on their mobile phone (eg. BusyBox e Mac address ghost for Android, which work only after unlocking the device via root, as I explained to you in more detail in my guide on how to clone WhatsApp) and manages to find out the MAC address of the victim's device (just go to the screen with the information in the settings device) can install a "cloned" version of WhatsApp and access his conversations.
Fortunately, this is a decidedly uncommon practice that requires a fair amount of technical preparation. Furthermore, at first the attacker must have the opportunity to tinker a lot with the victim's phone: in a first phase to discover the MAC address of the device and then to read the confirmation SMS necessary to activate the copy " cloned ”of WhatsApp on the other smartphone.
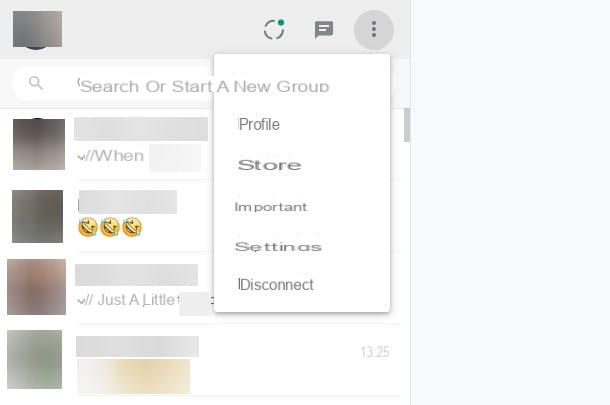
Until recently, another system adopted to spy on WhatsApp conversations without the victim's phone was to use the Web version of the messaging service or the computer client, which I told you about in detail in my post on how to use WhatsApp on PC, thanks to the function that allows you to stay connected, allowing the browser or program to store the user's identity and access conversations without requiring a new scan of the QR code. To date, however, such a technique can no longer be considered valid, as notifications relating to access are sent and biometric identification is required.
Monitoring of wireless networks

Many people have asked me if it is possible to spy on WhatsApp conversations without the victim's phone with applications that allow monitor all data passing over a wireless network (the so-called "sniffing"). The answer is no, at least no longer, based on what I explained to you in the passage at the beginning of the guide.
WhatsApp, therefore, is theoretically safe from monitoring Wi-Fi networks, but letting your guard down would be a serious, indeed a very serious mistake! So if you want to sleep even more soundly, start using one VPN. If you don't know what it is, it is a technology that allows you to browse online securely, encrypting your connection data and disguising your real location, via a virtual private network. There are many services of this type: among the most reliable and cheap I point out NordVPN (which I told you about in depth here) and Surfshark, which work on all major devices and operating systems.
To avoid problems, I recommend that you avoid connecting to public Wi-Fi networks and make sure you are using the most up-to-date version - and therefore also the one that should be more secure - of the application. This is a very simple precaution that can nevertheless avoid encountering "trouble". In this regard, you can read my guide on how to update WhatsApp.
Spy, anti-theft, parental control and access monitoring apps

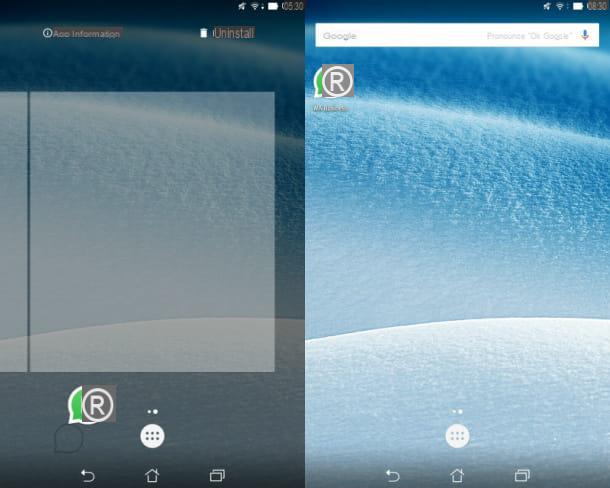
There are numerous in circulation apps that allow you to monitor, command and locate remote smartphones. Many of them are completely free and have the ability to hide, that is, they do not appear on the phone's home screen or on the screen with the list of all the apps installed on the device.
Such tools are born to allow the lawful monitoring of the user's smartphone, but taking into account their operation, they can be exploited as a means to spy on WhatsApp conversations remotely without the victim phone, provided that the attacker has had the opportunity to put his hand at least once to the cell phone of the person who intends to monitor or who has persuaded the victim remotely to download and install the tool to spy on another's WhatsApp, but passing them off as another type of content, perhaps by sending the relative link.
There are several apps that allow you to achieve this, as in the case of iKeyMonitor, one of the most popular spy applications that you can also try for free for a few days.
Furthermore, it must be said that anti-theft applications (those that allow you to locate lost mobile phones) and parental control services have such functions that could be used to capture screenshots and monitor most of the activities on the smartphone, such as for example Qustodio, available for both Android and iOS and Screen Time, also available for Android and iOS, which do not require advanced configurations and allow you to monitor and, if necessary, also to limit user activity.
I also point out that there are apps and online services that, using the public data of the well-known messaging service, allow you to monitor the hours of access to the service and that provide notifications relating to the activities carried out, all simply by typing the victim's phone number. Sometimes they stop working, but when available they can be particularly useful for spying on others' WhatsApp.
How to avoid spying on WhatsApp conversations without a victim phone

Based on what has been said in the previous lines, if you want to avoid being spied on WhatsApp conversations, it is essential that you put into practice some tricks, those indicated below, thanks to which you can manage your smartphone more conscientiously.
- Activate the screen lock on WhatsApp - not everyone is aware of it, but WhatsApp includes a feature that allows you to block access to the app via face or fingerprint and which turns out to be extremely to prevent other people from accessing their chats. To activate this function, go to the section Settings> Account> Privacy> Screen lock of WhatsApp and move to ON l'interruttore per activate the screen lock.
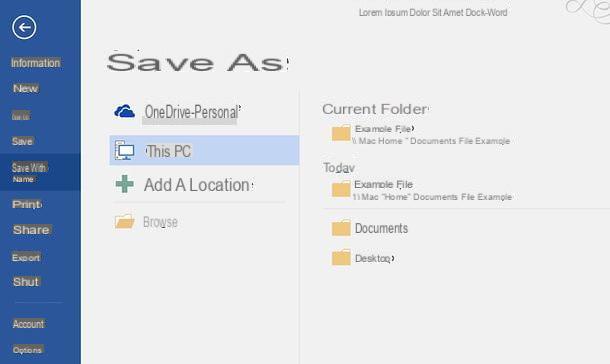
- I will post a sicuro PIN - a secure PIN can knock out most of the bad guys. For example, without accessing the main menu of the smartphone, it is not possible to install spy apps, for parental controls, etc. If you want to change the PIN on your smartphone, follow these steps: if you use Android you can do it by going to the section Settings> Security> Screen Lock device and selecting the item PIN (Or Sequence, if you want to use a gesture instead of the code); if you use a iPhone you have to go to the section Settings> Face ID / Touch ID and passcode of the device and selects the voice Change the code.
- Disable the display of SMS on the lock screen - by cloning the MAC address of the smartphone, an attacker could activate WhatsApp on his phone using his number. To do this, however, he should discover the verification code delivered via SMS to your mobile phone. By deactivating the display of SMS on the lock screen, it is possible to prevent this without first unlocking the smartphone. To do this, proceed as follows: if you are using Android go to the section Settings> Security> Screen Lock> PIN of the device, set a PIN and scegli di nascondere i contention sensitiv; if you are using a iPhone go to the section Settings> Notifications> Messages of the device and the spunta dalla voce Screen lock.
- I will verify the presence of applicazioni spia - if you suspect that there are spy applications on your smartphone, access the list of apps on the device and check the ones in use. To do this, do this: if you are using Android go to the section Settings> Apps> All of the device and delete all suspicious apps, then go to the menu Settings> Security> Device administrators and take a look at the list of apps that are allowed to control the system and if among them there is any that you have not authorized yourself, uncheck its name and uninstall it; if you are using a iPhone go to the section Settings> General> iPhone Space of the device and delete the apps that you think may be spying on you, by pressing on their name and on the option Delete app.
- Riattivare l'account in case of disattivazione - if someone activated WhatsApp on another mobile using your phone number, the service will stop working on your device. If you suddenly find yourself with the account disabled, immediately report it to WhatsApp support by contacting assistance.
Caution: spying on WhatsApp without the permission of the legitimate account owner is a serious breach of privacy! This tutorial has been written for informational purposes only and I do not take any responsibility for the use that will be made of the indications in it.