Index
Useful terms
Before getting to the heart of this guide and showing you some of the techniques used by cybercriminals to breach site security, I feel it is my duty to explain the meaning of some terms that I will use throughout this guide.
- Bow - this is the technical term to define a software programming error. Bugs in programs and apps are not always about security, however it is not uncommon to run into problems of this type. Typically, bugs are fixed by updates.
- Feat - is the term that identifies a program designed with the specific intent of exploiting a bug for the benefit of the criminal.
- 0-day - with this word “new” exploits are defined, not yet known to the security software houses, nor to the designers of the software involved.
- patch - is the solution released by programmers to fix a bug. Usually, patches are released as an update but, in some cases, they can be applied manually.
- Backdoor - literally "back door", it is an access channel that cybercriminals leave open, in order to access the server in a silent and undisturbed manner.
- Deface - is the practice implemented by cybercriminals to violate a site and distort its home page and / or its entire content.
- CMS - stands for Content Management System and identifies a set of programs that significantly simplify the creation of dynamic content (eg websites).
- Firewall - it is a system that protects data in transit to and from IT devices (servers, PCs, routers, smartphones, tablets and so on). It can be software or hardware.
How to pierce a website
The techniques used by cybercriminals for puncturing a website they are many and, very often, require a deep study of the "target". Therefore, hacking a site is neither simple nor immediate and, in most cases, the success of cybercriminals is a direct consequence of some carelessness on the part of whoever manages the site, or whoever hosts the machines on which it is run.
In the later parts of this tutorial, I will list some of the best known hack techniques from cybercriminals in mode remote, that is, without having physical access to the machine hosting the server (which, in practice, almost never happens).
Server vulnerability

Like everything that revolves around information technology, websites are also composed of files, which are generated and managed by a series of programs running on a computer (in this specific case, by a web server).
Generally, a server runs several dozen software at the same time and continuously exchanges data with the outside world: for this reason, a bug in one of the running applications is enough to jeopardize the integrity of the server itself, and of the data it contains. are hosted.
Typically, the most exploited vulnerabilities relate to the operating system running on the server, its core components or, sometimes, i device driver hardware. Designing the attack on a server is quite complex: to analyze the running software and any bugs present in them, it is necessary to bypass the security restrictions imposed by the firewall and any additional protection mechanisms.
Should the server actually be hacked, by means of a exploit or one 0-day, it is often possible to force the execution of arbitrary code, which could involve the hosted website, create a backdoor dedicated to future access, or perform other operations of this type. In severe cases, there could also be a genuine data leak.
How to defend yourself? Unfortunately, operating system bugs are quite frequent; it is true that, in most cases, developers are committed to release updates that can correct them promptly. Therefore, my advice is to always update the operating system to the latest version available or, at least, to promptly apply the security patches distributed by developers.
Vulnerability of installed components

The same argument seen a little while ago is valid not only for the operating system on board a Web server, but also for all the others installed programs on the machine: a bug in any software (even in the database manager!) could be enough to allow a cybercriminal to take control of the program itself, of the files / folders inherent to the website or, even worse, of the entire server.
How to defend yourself? Also in this case, my advice is to keep the server software constantly updated, also applying, as soon as possible, any security patches released by the developers.
Vulnerability of authentication systems

Another serious problem concerns the authentication systems in use for various websites: it may happen that an outdated protocol, a cracked encryption algorithm or, again, an unprotected password exchange, can allow a cybercriminal to acquire ownership of theadministration account of the portal or, even worse, of all the data present in the database and / or in the website folder.
Usually, this attacking technique has the direct consequence of the deface of the web portal, i.e. the complete distortion of the contents of the main page or other pages on the site. If the site management system allows, through its interface, to view the data saved in the memory, a criminal could have free access to the latter as well.
As defend yourself? First, it is imperative to protect data in transit to and from the encrypted website SSL, configuring the server to use the secure connection protocol HTTPS. Secondly, if the site contains login pages, it is advisable to verify that they function correctly and that the relative code does not give rise to unexpected events, which could endanger the integrity of the site.
Finally, of course, all access to the site must be protected with secure passwords that are difficult to guess, but I don't think there is much need to say about this: it should be the ABC of life on the Web.
Vulnerability of CMS and plugins

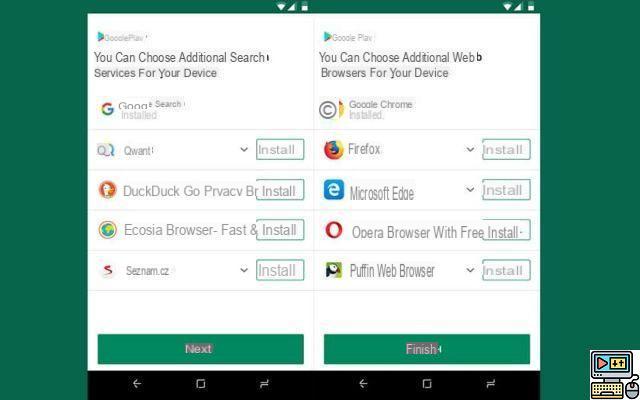
Numerous Web sites existing on the Net are created using CMS, that is, through systems that allow you to create, update, manipulate and manage simple and complex portals, without the need to manually write the code of each single page, for example the very famous WordPress.
CMSs are also programs and, unfortunately, they can be subject to bugs and malfunctions of various types. In particular, the security problems of open source CMS are very often disclosed to the community: if this, on the one hand, helps developers to implement security patches as quickly and effectively as possible, on the other hand it helps cybercriminals. to make specific exploits and 0-days for a given bug.
Unfortunately, these exploits are usually used (successfully) on all those sites built using outdated CMS, with all the obvious consequences of the case. So, if you were, your intention was to understand how to pierce a WordPress site or any other portal created through a CMS, the answer is soon given: just analyze the version of the CMS in use and do a little research on the Net about the active vulnerabilities. A bit of experience and a lot of patience could do the rest!
The same goes for the Plugin installed in the various CMS: a bug within an add-on could compromise the stability of the entire site and its management system, even if the latter is natively free from bugs.
How to defend yourself? Also in this case, updating is the key word: if you manage a website, it is very important to be well aware of its implementation methods, the CMS in use and any plugins installed, and to constantly inquire about the integrity of these components. In this way, you can become aware of any vulnerabilities before criminals even start exploiting them, applying the necessary updates and patches in the shortest possible time.
How to pierce a site