Spy on WhasApp from PC "sniffing" wireless networks

As I mentioned in the introduction, WhatsApp uses a technology of end-to-end encryption (i.e. from point to point) call Textsecure2 in which the keys generated automatically by the app ensure the secrecy of the conversations. To put it simply, messages arrive on users' smartphones and service servers in encrypted form and only legitimate senders / recipients can see the content. However, this does not completely put cybercriminals out of action.
As mentioned earlier, WhatsApp is an application closed source and therefore we cannot thoroughly examine its source code. Not being able to perform such an operation, we cannot know if end-to-end encryption is applied correctly or if, for example, it is disabled in some countries at the specific request of local governments.
In April 2015, Heise researchers used the software Wireshark to "Sniffing" WhatsApp communications and they found that only the Android version of the application used end-to-end encryption. Other versions of the app used encryption based on the RC4 protocol, which only works on exit and is notoriously vulnerable to attacks by cybercriminals.
Following the publication of the study, the developers of TextSecure made it known that the adoption of end-to-end encryption by WhatsApp would take place gradually3, therefore not on all platforms at the same time but a little at a time. This means that while Android> Android communications were 100% protected (or so it seemed), those to and from iOS, Windows 10 Mobile, etc. they could still be subject to easy interceptions.
At present, end-to-end encryption has been implemented on all platforms for which the messaging application is available but, as it is not possible to access the WhatsApp source code, we cannot know if the use of this type of encryption has been applied to perfection and, therefore, we cannot be absolutely sure that it is impossible to intercept users' messages with Wireshark or other software to sniff wireless networks.
The only precautions that we users can put into practice to protect ourselves is do not connect to public wireless networks which, as known, are the favorite hunting ground for "sniffers", and use the services of VPN, Such as NordVPN (which I told you about in depth here) and Surfshark (more info here), which encrypt all connection data and hide the user's geographical position, protecting him from any tracking.
Spy on WhatsApp from PC via WhatsApp Web
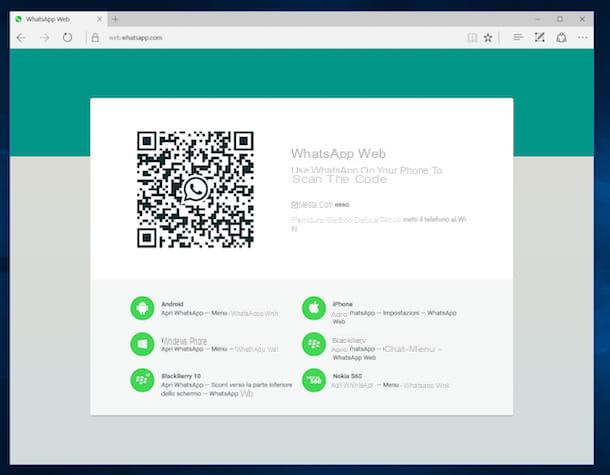
Wireless sniffing has been potentially knocked out by end-to-end encryption, but sadly, there are other ways to spy on WhatsApp from PC. One of them has to do with the identity theft via WhatsApp Web, the official WhatsApp service that allows you to send and receive messages from your PC. I also told you about it in my tutorial on WhatsApp for PC, remember?
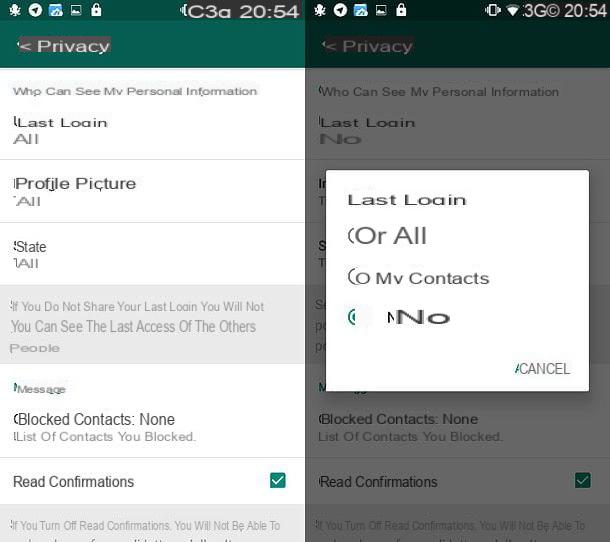
WhatsApp Web works by using the smartphone as a "bridge", so it can only be used if the mobile phone on which the application is installed is switched on and connected to the Internet, however it has two characteristics that make it particularly attractive to malicious people: it is able to memorize the user's identity (just check the box Stay connected after logging in for the first time) and works regardless of the connection used on the mobile phone (the phone may also be far from the computer and the service is equally accessible). It must be recognized, however, that perpetrating spying actions via WhatsApp Web has become (fortunately) much more complex, as the service sends notifications at every access.
This does not mean that an attacker could potentially steal your smartphone, use it to access WhatsApp Web on his computer (or tablet) and gain free access to your conversations. To prevent this risk, do not lend your phone to strangers, do not leave the device unattended and check the WhatsApp Web sessions active on your account.
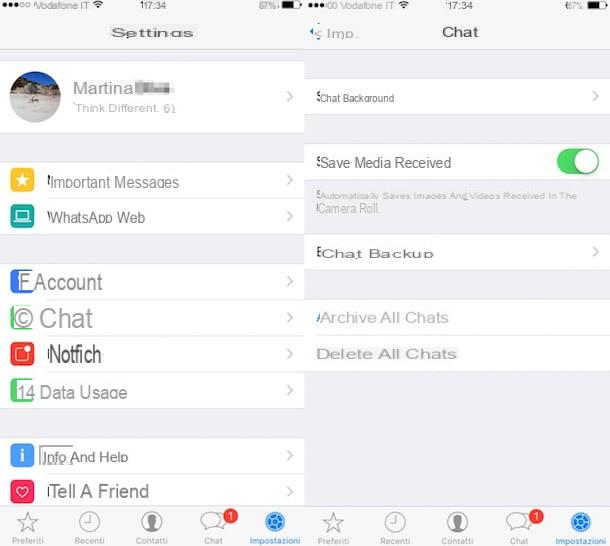
If you don't know how to check active WhatsApp Web sessions, open WhatsApp and go to the menu Settings> WhatsApp Web / Desktop. You will be shown a list of all the browsers from which you can access your messages, complete with the last accesses. In case you notice any suspicious activity, press the button Disconnect from all computers / Disconnect from all devices and all computers associated with your WhatsApp account will lose access.
Fortunately, such systems can be made impossible to implement if you activate biometric recognition protection on your device. In this case, in fact, if a face or fingerprint unlock is set on your smartphone / tablet, this option is also requested when connecting with WhatsApp Web / Desktop, for the purpose of confirming the identity of the person who is activating the service.
Spy on WhatsApp from PC with spy applications

Another danger you must be on guard against are the so-called spy-applications, i.e. applications that are able to monitor all the activities carried out on the smartphone, geographically locate the device and capture snapshots of its screen, such as the very famous iKeyMonitor I told you about in another post. This information is then sent remotely to the attackers and / or can be viewed via a web panel whose login details are known only to those who have installed the application on the phone. Parental control apps (such as Qustodio o Mobile Fence, which I told you about in this guide)
How can you prevent someone from installing spy applications on your smartphone and controlling your conversations on WhatsApp through them? To begin with, don't lend your smartphone to people you don't trust. Secondly, do not unlock your device via procedures such as the root or jailbreak, because they would make him particularly vulnerable. Other importantly, protect your device with a secure and hard-to-guess unlock code. If you don't know how to set up a passcode, follow these steps.
- Android - go to the menu Settings> Security> Screen Lock I will select the voice PIN from the screen that opens.
- iPhone - go to the menu Settings> Touch ID and Passcode (o Face ID and Code) and select the item Change codice. If your "iPhone by" supports unlocking via fingerprint sensor or facial recognition, prefer the latter.
I also advise you to check the apps installed on the device, to verify that there are not any "suspicious" ones. To do this, go to Settings> Apps> All (on Android) or in Settings> General> iPhone Free Space (on iPhone) and check which apps are installed.
It must be recognized, however, that many spy applications are able to hide and are not displayed in the device menus and to find them you need to use special codes (as I have well explained to you in my guide on how to find spy apps). How can you use these codes? I'll explain it to you right away.
- Start the browser of your smartphone and try to connect to the addresses localhost: 4444 or localhost: 8888, used by many spy apps to hide their configuration panel.
- Start the dialer, the screen from which you enter telephone numbers, and enter the code * 12345, so as to access the configuration panel of an app-spy possibly installed on the phone.
- A device is possible Android submitted to root, I recommend you boot SuperUser / SuperSU and check for any spy apps among those that have obtained root permissions. If you find any, immediately revoke the permissions in question.
If from your "investigations" you find that someone is actually monitoring your activities, I suggest you format the device and delete all the data in it, as I explained in the guides on how to reset Android and how to reset iPhone.
- WhatsApp network forensics: Decrypting and understanding the WhatsApp call signaling messages (in lingua inglese). ↩
- Click here to find out all the technical details on how TextSecure encryption works (in English). ↩
- Here is the response of the developers of TextSecure to the test conducted by Heise (in English). ↩